Secure Networking for Openshift
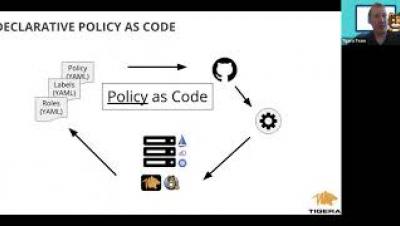
The Kubernetes network model defines a flat network in which pod connectivity is unimpeded, with no restrictions on what traffic is allowed to or from each pod. To make a cluster production ready you need to make this networking secure. Network Policy is the primary tool for doing this and is essential to understand before considering moving a cluster to production.