Elastic Global Threat Report Breakdown: Credential Access
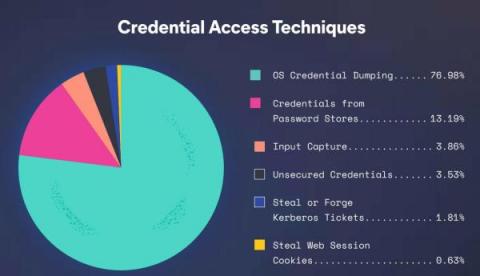
In the second part of our breaking down the Elastic Global Threat Report series, we’re focusing on the credential access tactic, which was the third-most common category of behavior we observed. Roughly 10% of all techniques we saw involved one form of credential theft or another and dissecting this class of behaviors is helpful both to improve our understanding of threats and to better understand enterprise risks.