ISO 42001:2023 and the New Reality of Cloud AI Data Risk
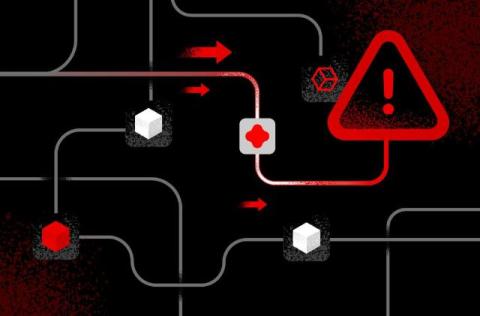
As organizations accelerate adoption of AI systems, the scope of data security has dramatically expanded. Sensitive data is no longer simply stored. It is continuously accessed, transformed, and moved across cloud services, APIs, and AI pipelines. For use cases from model training to inference, AI systems depend on dynamic data flows that introduce new and often unseen risks.