Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
ReBAC to the Future! Building Policy on Neo4j Data with Enterprise OPA
Relationship-based Access Control (ReBAC) is a common requirement when applying Policy as Code controls in modern applications. Consider sharing a document with a collaborator in a different organization. As the collaborator is in another organization, it might be hard to grant them a pre-defined internal role without granting more permissions than needed – if indeed an external identity can be bound to an internal role at all. This is where ReBAC comes in.
Why You Need Continuous Monitoring in Microservices
The microservices architecture is a software development strategy in which applications are broken down into smaller components called microservices. Each microservice is responsible for a specific task or business function and communicates with other microservices through application programming interfaces (APIs). Effectively managing a microservices application requires monitoring, much like any other IT infrastructure.
The never-ending story: Microsoft AI team accidentally exposed 38 Terabytes of internal data
The accidental sharing of cloud access is an all-too-familiar story. In one latest incident, Microsoft’s AI research team accidentally exposed to the public 38 Terabytes of private data including internal messages, private keys, and passwords, according to a recent report . And all it took to cause this gigantic exposure was a few errant clicks in a configuration menu.
How to express OR in Rego
One of the most common questions people new to Open Policy Agent (OPA) and Rego ask is about how to express logical “OR” in the language. While there is no “OR” operator, Rego has no shortage of ways to express that, with some being more obvious than others. In this blog, we’ll take a look at the most common ways to express OR, and weigh the virtues of each method against the others. Hopefully you’ll learn a few tricks along the way.
What Are the Most Common Security Risks of Cloud Computing?
Identifying and understanding the most common cloud security risks is crucial to a successful cloud computing adoption strategy. Organizations migrating to the cloud continually face new threats and discover vulnerabilities that were not present when they operated software deployed on-premises. According to IBM’s Cost of a Data Breach report, almost half of all data breaches are happening in the cloud, with attacks on systems hosted on public clouds costing an average of $5.02 million.
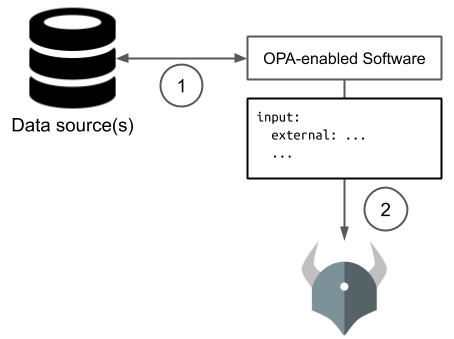
THEY DID WHAT!? Auditing a security breach using Enterprise OPA decision logs and AWS Athena
You will learn how to use the Enterprise OPA Enhanced Decision Logs feature to configure Enterprise OPA (EOPA) to upload decision logs to an AWS S3 bucket so that they can be queried using AWS Athena. In mid to large sized deployments of EOPA, immense quantities of decision logs can be generated, necessitating big data tools such as Athena. This can be useful for security breach auditing, auditing access decisions, and for business intelligence in general.
How to Secure Communication Between Microservices
The migration to microservice architecture from monolithic applications is happening en masse as enterprises realize its scalability and efficiency benefits. According to an IBM report1, 56% of nonuser organizations plan on adopting the microservice architecture by 2023. Breaking an application into small, loosely coupled services lets independent teams quickly design and deploy these components.
Real-time authorization with Enterprise OPA and gRPC
In this article, you will learn about how to achieve high-throughput, real-time authorization. You should gain a basic understanding of the different protocols for interacting with the Open Policy Agent (OPA) and Styra Enterprise OPA APIs, as well as how and when to use different options. We will also cover the strengths of different protocol choices, and where they may make sense in your system architecture.
OPA in Production - How Reddit and Miro Built Enterprise Authorization with OPA
Two web-scale companies have recently shared how they solved mission-critical authorization challenges using Open Policy Agent (OPA). These accounts validate the value of what we’ve built with OPA and give important blueprints for engineers looking to address similar challenges. We consider these required reading for anyone considering or using OPA at scale. In this post we review these two case studies to highlight common patterns and important differences.