Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
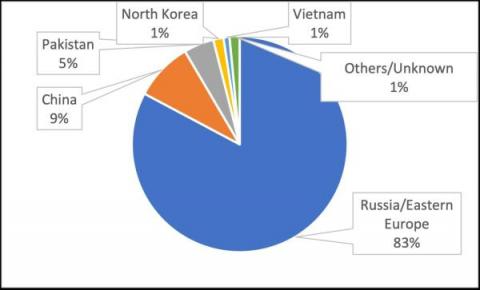
Cyberthreat Trends in 2022H1: Threat Actors Observed, New Malware and Active Hacking Groups
In our companion blog post, Vedere Labs analyzed the main ransomware trends we observed in the first half of 2022, including state-sponsored ransomware, new mainstream targets and evolving extortion techniques. Ransomware is the main threat targeting most organizations nowadays. However, three other notable cyberthreat trends also evolved during this period: Below we analyze each of these trends in more detail.
6 Ways Hackers Can Bypass MFA + Prevention Strategies
Organizations must implement effective account protection measures or put themselves at heightened risk of data breaches and other serious cyber attacks, such as ransomware injections. Multi-factor authentication (MFA) is a crucial component of any organization’s cybersecurity program. MFA adds an additional layer of security, helping prevent hackers from gaining unauthorized access to sensitive data.
Recent Phishing Attack Highlights How Hacks Are Changing
Apple, Google Patch iOS, Chrome Zero-Days Exploited by Hackers
Read also: Microsoft disrupts a phishing operation targeting NATO countries, the use of wiper malware expands beyond Ukraine, and more.
How Hacking Has Evolved Over Time
Bugcrowd Taps Top Hackers for Live Hacking Event with Indeed at 2022 Black Hat Conference
Controlling your server with a reverse shell attack
Creating and running an application in your favorite language is usually pretty simple. After you create your application, deploying it and showing it to the world is also quite straightforward. The last thing you need is someone to take over your system and fully control your brand new application. In this article, I’ll explain how this can happen with a reverse shell attack. Note that the code examples in this article are for educational purposes only.
HackerOne: Hacked from the Inside
When it comes to hackers exploiting vulnerabilities in their software, organizations have two choices: They can fight the multi-headed hydra — or they can try to buy them off. And thus was born the bug bounty. Of course the situation is a bit more complicated than that, but ever since Peiter C.
How can we turn a hacker's toolkit against them?
Hackers use many tools at each stage of an attack. These tools are often readily available online, both free of charge and to buy, and easy to use for non-technical cybercriminals. Understanding a hacker’s tools and tactics is essential for cyber security practitioners and vendors aiming to build effective defenses and stay one step ahead of a quickly evolving host of cyber threats.