Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
The Dangers of Rushing into AI Adoption: Lessons from DeepSeek
As organizations race to adopt the latest advancements in artificial intelligence, DeepSeek serves as a cautionary tale about the potential dangers of rushing into the hype cycle without adequate consideration of security and ethical implications. DeepSeek, a Chinese AI startup, has been identified as having several significant security risks and vulnerabilities that could pose threats to both the company and its users.
Sensitive Data Leaks from AI Model Use | The 443 Podcast
How are you using ChatGPT at work? On this week's episode of, Corey Nachreiner and Marc Laliberte dig into a report on sensitive data leakage caused by AI model use. They also cover a recent report that highlights a drop in ransomware payments in 2024, as well as a recent attack targeting ASP.NET web servers.
CISA Reports a Massive Spike in API Security Risks #CISAReport #ProtectAPIs APIExploit
In 2024, API-related vulnerabilities on CISA’s Known Exploited List jumped from 20% to 50%, making APIs a prime target for attackers. This sharp increase highlights the critical need for a dedicated API security strategy in 2025. Don’t wait—invest in API security today.
Artificial Intelligence Security Posture Management (AISPM): An Explainer
As AI Agents continue to revolutionize everything about how business is done, ensuring the security of these agents has become paramount. While organizations have rushed to adopt DLP processes and whitelist/blacklist policies to block the use of malicious prompts, it’s worth noting that DLP and firewalls have been around for a very long time and have proven limited in mitigating the risks of users copy/pasting sensitive information onto the internet.
Runtime security in cloud environments: what you need to know
Unlike static environments, cloud workloads are constantly shifting, with containers and virtual machines spinning up and down, and crucial sensitive information flowing dynamically across multiple platforms. Recent incidents, such as the increase in container-based malware infections and cloud misconfigurations resulting in major data breaches, have highlighted the need for runtime security.
Generating Code with ChatGPT...
Snyk helps you find and fix vulnerabilities in your code, open-source dependencies, containers, infrastructure-as-code, software pipelines, IDEs, and more! Move fast, stay secure.
IIoT Security Threats Reshape Factory Protection Strategies
Modern factories are increasingly relying on Industrial Internet of Things (IIoT) solutions. This shift is beneficial in many regards, including higher efficiency and transparency, but it also introduces unique cybersecurity concerns. Better vulnerability management for IIoT systems is essential if companies hope to make the most of this technology. The White House’s 2024 cybersecurity report named critical infrastructure risks and supply chain exploits as two of the top threats facing the U.S.
Automatic Audit Logs: new updates deliver increased transparency and accountability
Audit logs are a critical tool for tracking and recording changes, actions, and resource access patterns within your Cloudflare environment. They provide visibility into who performed an action, what the action was, when it occurred, where it happened, and how it was executed. This enables security teams to identify vulnerabilities, ensure regulatory compliance, and assist in troubleshooting operational issues. Audit logs provide critical transparency and accountability.
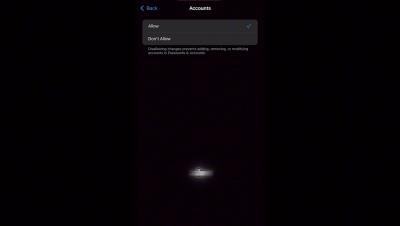
How to avoid being targeted by a Mobile application Data Breach
Our lives are increasingly intertwined with technology, and apps have become indispensable tools in our daily routines. From ordering groceries with just a few taps on our phones to connecting with loved ones across the globe through video calls, apps have revolutionized the way we live, work, and play. We rely on a variety of apps for everything from productivity and entertainment to health and fitness. For example, we use restaurant discount apps to discover exciting new diners and snag amazing deals on delicious meals.