Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
The Role of UEBA in Zero Trust Security
As cyber threats have grown in sophistication and frequency, a paradigm shift in security strategy has become imperative. This shift has given rise to the Zero Trust Security Framework, an approach that challenges the very foundation of trust in network security. User and Entity Behavior Analytics (UEBA) steps into the spotlight as a dynamic force that complements and enhances the Zero Trust Security framework. Let’s discover how UEBA can help organizations achieve zero trust security!
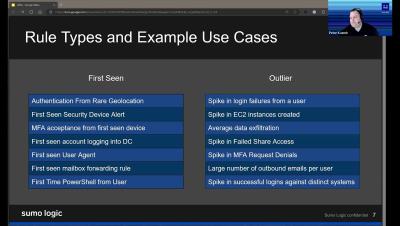
Sumo Logic Customer Brown Bag - Security - UEBA - September 19th, 2023
Operationalizing Advanced UEBA: Detection Scenarios and UCI Alerts
Netskope has recently released two exciting enhancements to our Advanced UEBA product. The enhancements are: Together, these two new features streamline operationalization of Advanced UEBA by providing operators alerts when it identifies users exhibiting risky behavior and an at-a-glance summary of the risky activity observed for each user.
The Thin Line Between User Behavioral Analytics and Privacy Violation
Technology has supercharged marketing. The vast data at marketers' disposal provides unparalleled insight into what customers want, why they want it, and how they use products and services. Behavioral analytics benefits businesses and consumers; it allows companies to drive sales and increase conversion rates while providing customers services tailored to their wants and needs.
Unlocking the Potential of UEBA With Logsign
In today's cybersecurity landscape, traditional security tools alone are inadequate in protecting organizations from advanced threats like data breaches, insider risks, and more. To effectively address these challenges, organizations require a comprehensive solution with UEBA (user and entity behavior analytics) capabilities. Let's discover the benefits of UEBA, and the unparalleled impact Logsign’s Unified Security Operations Platform has on UEBA.
UEBA Trends: What's New and What's Next
User and entity behavior analytics (UEBA) is a technology that analyzes the behavior of users and devices on a network to detect anomalies and threats. UEBA can help security teams identify and respond to malicious activities, such as insider threats, compromised accounts, data breaches, ransomware attacks, and more. In this article, we will briefly summarize the latest trends in UEBA and its potential transformation.
UBA vs UEBA - Decoding the Differences
One of the most important aspects of cybersecurity is monitoring and detecting threats that may compromise the security and integrity of your company. However, not all threats are easy to spot or prevent with traditional security tools. That’s why many cybersecurity enthusiasts, professionals, and IT units of companies are curious about UBA and UEBA. But what is the difference between UBA and UEBA?
SIEM and UEBA: A Match Made in Cybersecurity Heaven
SIEM and UEBA are complementary solutions that can work together to provide a comprehensive view of network activity and enhance the threat detection and response capabilities of cybersecurity teams. By integrating SIEM and UEBA, organizations can benefit from.
The Science of Behavioral Biometrics in UEBA Solutions
As the world becomes increasingly digital, cyber-attacks are becoming more sophisticated, and traditional security measures like firewalls and passwords are no longer enough to protect sensitive data. Fortunately, advancements in technology have given rise to User and Entity Behavior Analytics (UEBA), a behavioral biometrics-based approach that can effectively detect and prevent cyber threats. In this blog post, we will explore the role of behavioral biometrics in UEBA.