Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Rezilion
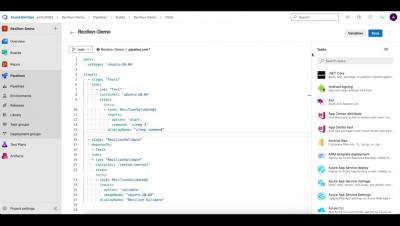
Deliver Secure Products with Rezilion Azure DevOps Integration
With an unprecedented amount of product releases, developers and security teams are both faced with the challenge of balancing security with on-time delivery. Without critically-needed automation tools to detect, prioritize, and address security risks, DevOps teams end up patching vulnerabilities that do not pose actual risks. This slows down development, leaves organizations vulnerable, and causes friction with DevOps’ aggressive release cycles and product security teams.
The Time is Now to Eliminate Vulnerability Backlogs
There are three things in life you can count on: death, taxes, and vulnerability backlogs. Eliminating them has become a major thorn in the side of DevSecOps professionals because it’s not always clear which ones need to be addressed and how quickly. That’s the key: being able to assess, prioritize, and then remediate vulnerabilities.
Organizations Want to Adopt DevSecOps. What's Getting in Their Way?
Security leaders are eager to move to a DevSecOps approach—and why wouldn’t they be? DevSecOps has been emerging as a key component in organizations’ efforts to build strong security into all the software products they deliver. The adoption and implementation of the DevSecOps methodology involves multiple facets of organizations and brings together security and development professionals in a collaborative mission to deliver products that are both high in quality and secure.
Dynamic SBOM = SBOM + VEX
In recent months there has been a lot of discussion around the importance of Software Bills of Materials (SBOM) and Vulnerability Exploitability Exchange (VEX) when it comes to managing software vulnerabilities. Organizations can combine the SBOM and VEX to get a more contextualized view of the actual risk present in their environment. In this blog post, we examine how SBOMs and VEX do not need to be 2 artifacts.
Report: Organizations Are Open for Exploit By Taking Too Long to Patch
New research from the Ponemon Institute uncovers a troubling trend when it comes to risk management. That is, organizations are simply not patching software vulnerabilities fast enough to keep up with the demand for remediation. This can lead to cybersecurity attacks that could spell trouble for businesses as they try to ward off incidents that result in significant damage to their operations.
Rezilion and Ponemon Release New Report; Finds Thousands of Hours Lost to Vulnerability Backlog Management Due to Lack of Prioritization and Automation
It's About Time: Ponemon Report Reveals How Many Hours Organizations Are Losing to Vulnerability Management
If there is one thing we all want more of in life, it’s time. And there are few places where we are more pinched for time than on the job. With so many tasks and deliverables to get done, it rarely seems like we have enough hours in the day to tackle it all. In the world of software security, developers experience this daily as the work to ship code without vulnerabilities.
VEX, A Primer
VEX is an acronym for Vulnerability Exploitability eXchange and was developed by the National Telecommunications and Information Administration (NTIA). According the guidance provided by NTIA , the primary use cases for VEX are to provide users (e.g., operators, developers, and services providers) with additional information on whether a product is impacted by a specific vulnerability in an included component and, if affected, whether there are actions recommended to remediate.