Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Secure Networking for Openshift
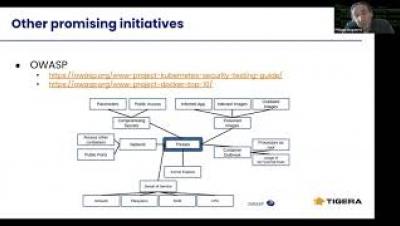
Kubernetes Q3-2020: Threats, Exploits and TTPs
Kubernetes has become the world’s most popular container orchestration system and is taking the enterprise ecosystem by storm. At this disruptive moment it’s useful to look back and review the security threats that have evolved in this dynamic landscape. Identifying these threats and exploits and being a proactive learner may save you a lot of time and effort…as well as help you retain your reputation in the long run.
Network Policy with GKE
How to Secure Mixed Linux/Windows Clusters with Calico Policy
Kubernetes Security - Intrusion Detection and Mitigation
Achieving CI Velocity at Tigera using Semaphore
Tigera serves the networking and policy enforcement needs of more than 150,000 Kubernetes clusters across the globe and supports two product lines: open source Calico, and Calico Enterprise. Our development team is constantly running smoke, system, unit, and functional verification tests, as well as all our E2Es for these products. Our CI pipelines form an extremely important aspect of the overall IT infrastructure and enable us to test our products and catch bugs before release.
Self-Service Network Security for Kubernetes
The New Model for Network Security: Zero Trust
The old security model, which followed the “trust but verify” method, is broken. That model granted excessive implicit trust that attackers abused, putting the organization at risk from malicious internal actors and allowing unauthorized outsiders wide-reaching access once inside. The new model, Zero Trust networking, presents an approach where the default posture is to deny access.
Mitigating the Risks of Instance Metadata in AWS EKS
Compromising a pod in a Kubernetes cluster can have disastrous consequences on resources in an AWS Elastic Kubernetes Service (EKS) account if access to the Instance Metadata service is not explicitly blocked. The Instance Metadata service is an AWS API listening on a link-local IP address. Only accessible from EC2 instances, it enables the retrieval of metadata that is used to configure or manage an instance.