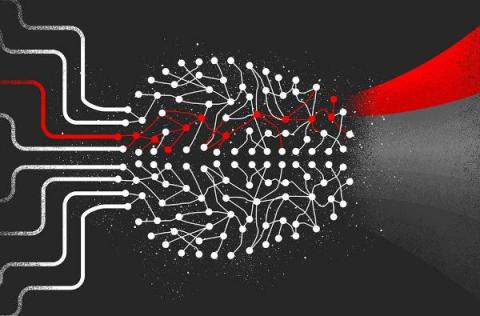
How CrowdStrike Uses Similarity-Based Mapping to Understand Cybersecurity Data and Prevent Breaches
The CrowdStrike Falcon® platform harnesses massive amounts of data, collected from trillions of events that are routinely captured on a daily basis. This data must be organized in a way that facilitates the confluence of disparate representations before the inherent value of that data can be realized.