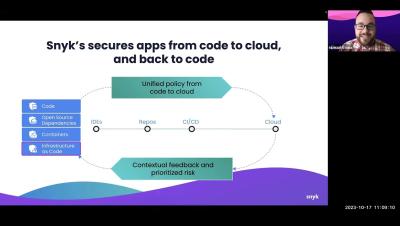
Why you need a security companion for AI-generated code
Everyone is talking about generative artificial intelligence (GenAI) and a massive wave of developers already incorporate this life-changing technology in their work. However, GenAI coding assistants should only ever be used in tandem with AI security tools. Let's take a look at why this is and what we're seeing in the data. Thanks to AI assistance, developers are building faster than ever.