Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
The Cybersecurity Investment Most Organizations Are Failing to Secure
Welcome to the 2025 Identity Security Landscape rollout—and to the “it’s complicated” phase of our relationship with AI. Each year, CyberArk surveys security leaders across the globe to understand their top identity security concerns. This year, AI delivered the trifecta: attack weapon, defense tool and risk multiplier.
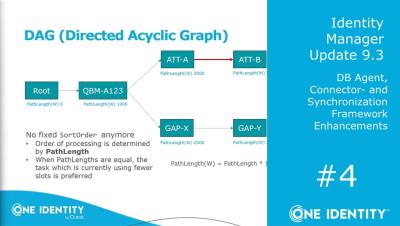
Identity Manager | Update 9.3 | #4 DB Agent, Connector- and Synchronization Framework Enhancements
Training Video Series: Identity Manager Update 9.3 - Part.
KubeCon Europe 2025: Why Identity is the New Backbone of Secure Infrastructure
The standout themes at KubeCon + CloudNativeCon Europe 2025 in London strongly centered on how identity is rapidly becoming the linchpin for securing cloud-native infrastructure. The recurring theme I saw wasn’t just Kubernetes innovation—it was the rising urgency of securing the who behind every action across platforms, clusters, services, and tools.
Identity Manager | Update 9.3 | #3 IGA-, Attestation-, IT-Shop Enhancements, SAP Compliance
Training Video Series: Identity Manager Update 9.3 - Part.
Drupal Single Sign On - Microsoft Entra ID as OAuth Provider
This video will walk you through the steps required to configure Microsoft Entra ID as OAuth Provider and Drupal as OAuth Client. The module allows users to log in to the Drupal site using their Microsoft Entra ID credentials. Chapters: Don't forget to subscribe to our channel and click on a bell icon to get notifications about new uploads.
Secure Azure AD Multi-Tenant SSO for WordPress Businesses
In this blog, we’ll show you how to simplify Azure AD Multi-Tenant authentication using the miniOrange OAuth SSO plugin. You’ll learn how to get secure, seamless Azure AD SSO working for multiple organizations—fast and hassle-free.
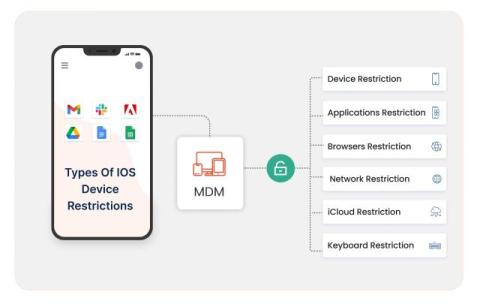
MDM Restrictions for iOS Devices: Lock Down, Secure & Empower Your Business
Managing iPhones and iPads across your organization can feel like a never-ending challenge. From misuse of apps to potential data leaks—businesses need a better way to stay in control. In this blog, you’ll learn how iOS MDM restrictions can help you apply smart policies, secure devices, and streamline mobile operations.
Modern Cybersecurity Strategies for Linux Servers
Linux servers have become widely adopted across organizations of all sizes. However, the frustrations of integrating these servers have left organizations struggling to implement strong security procedures, which cyberattacks have exploited for years. For instance, the “perfctl” malware family has been targeting Linux servers and attempting to escalate privileges for over three years.
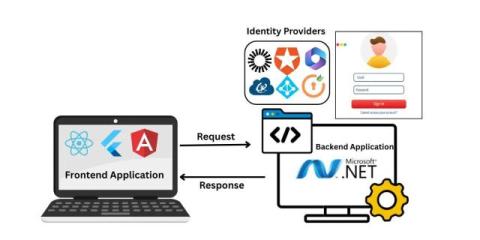
Secure Your Decoupled .NET Apps with SAML SSO
Simplify Authentication Across Your.NET Applications.Eliminate repeated logins with SAML Single Sign-On (SSO) built for decoupled.NET apps. Let users log in once and securely access all your applications—streamlining access while ensuring enterprise-grade security and a seamless user experience.