Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
This Feels Scripted: Zeek Scripting and Splunk
I originally planned to write this story as a follow-up to another blog that SURGe released for CVE-2022-3602 and CVE-2022-3786 (aka SpookySSL). That blog mentions that we weren’t able to test with any malicious payloads yet, and as things go… After releasing that blog, we came across proof-of-concept exploits that weren’t detected by our searches.
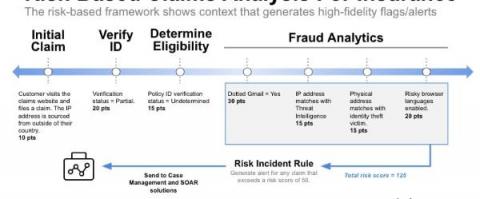
Reputational Risk Mitigation
Simplify your procurement process and subscribe to Splunk Cloud via the AWS marketplace Unlock the secrets of machine data with our new guide All companies want to protect their reputation as any mishandling of it, either self-inflicted or via outside forces, can have a devastating impact. Mitigating reputational issues involves mitigating the risk that leads to them.
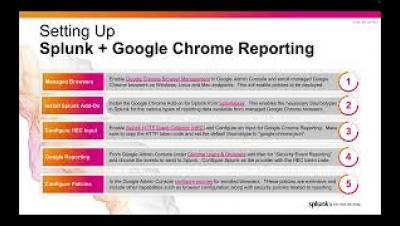
Extend endpoint visibility with Google Chrome and Splunk security
Inside the Mind of a 'Rat' - Agent Tesla Detection and Analysis
Agent Tesla is a remote access trojan (RAT) written for the.NET framework that has knowingly been in operation since 2014. Threat actors behind this malware have leveraged many different methods to deliver their payload over time including macro enabled Word documents, Microsoft Office vulnerabilities, OLE objects and most recently, compiled HTML help files.
Network Security 101: A Brief Intro to Securing Networks
We live in a world of rapid technological advancements. Technologies such as big data, the internet of things (IoT) and artificial intelligence have created a world full of opportunities and solutions. However, it has also opened doors to increased threats, cyberattacks and network vulnerabilities. This post will explain network security, including relevant concepts and issues, as well as best practices that can your organizations secure all your networks and surfaces.
Cyber Kill Chains Explained: Phases, Pros/Cons & Security Tactics
Sometimes referred to as CKC or the cyberattack lifecycle, the cyber kill chain is a security defense model developed to identify and stop sophisticated cyberattacks before they impact an organization. Typically comprised of seven steps, a cyber kill chain model breaks down the multiple stages of a cyberattack, allowing security teams to recognize, intercept or prevent them.
Devo Multitenancy Provides Fast, Secure, Self-Service Access to Data Across Multiple Tenants
Security teams need the ability to model their complex organizations by splitting data across multiple tenants while maintaining complete visibility throughout the entire infrastructure. At the same time, they must keep data segregated to maintain security and meet data residency and compliance requirements.