Anomaly Detection with Machine Learning to Improve Security
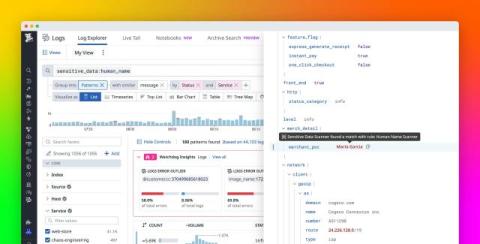
Being a security analyst can feel like being trapped in a Where’s Waldo book. You can find yourself staring at a data stream looking for something that “isn’t like the others.” However, as your organization collects and correlates more data from the environment, finding the Waldo can feel overwhelming. In a modern IT environment, organizations have hundreds or thousands of devices, users, and data points that they need to correlate so they can identify normal network activity.