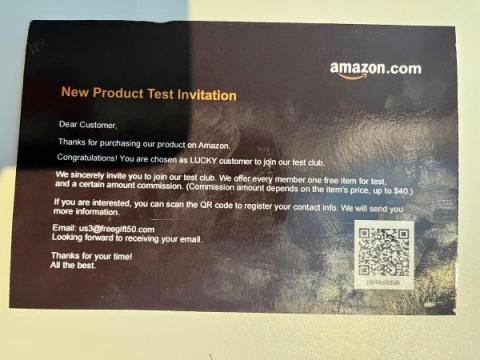
Nearly One-Quarter of Financial-Themed Spam Emails are Phishing Attacks
While spam tends to be dismissed as being more an annoyance, new research shows that there is a very real and ever-present threat in emails that are marked as “spam”. I’ve written plenty about phishing attacks that target bank customers. It’s nothing new. What’s interesting is a recent article by security researchers at BitDefender where banking-related phishing attacks are considered spam.