Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
The rising bot threat to media, marketplaces and video gaming
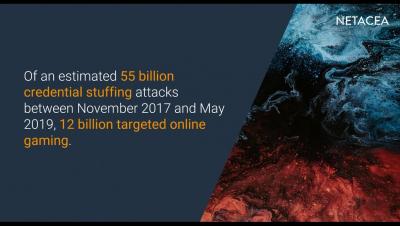
Over recent years, botnet attacks have hit platforms hard with their mass destruction approach to cyber-attacks. However, the tide has turned, and automated bot technology now makes targeted attacks infinitely quicker and simpler to carry out, exposing online gaming and streaming businesses to greater threats. The challenge lies in accurately identifying these highly targeted automated bot attacks that are designed to hide in plain sight, masquerading as genuine users, before they can carry out malicious activity such as credential stuffing, fake account creation and scraping.
Are APIs the Gateway for Credential Stuffing Attacks?
FinTechs have emerged as the digital-first answer to transforming the banking industry. Legislation such as the EU’s PSD2 and the UK’s Open Banking have cemented their place in the financial services environment, while removing much of the red tape that surrounds financial services to encourage collaboration and ensure security by design. Much of this collaboration is facilitated by open APIs, but what do we know about the API layer and security vulnerabilities that threaten your FinTech when it is exposed?
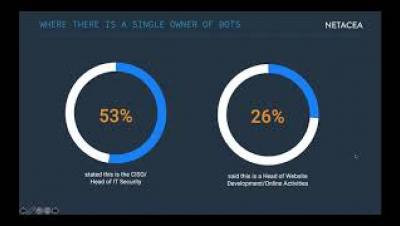
Who is responsible for bot management | Webinar series part-3
At Netacea, we wanted to know just how aware businesses are of bots and if they fully understand the threat to their organisation. Which roles are responsible, how confident are they in their bot mitigation strategies, and how well-placed is this confidence? We surveyed 200 enterprise businesses across travel, entertainment (including online gaming and streaming), e-commerce and financial services to get a broad picture of how bots are understood and protected against.
The State of Bot Attacks in 2020 | Bot Management Review Series Part 1
In 2020 the poor security of other businesses is now very much, your problem. While you might be protecting your customers’ credentials with the best possible security, lax measures elsewhere mean those very same credentials are readily accessible for purchase. Increasingly sophisticated bots are used to validate the millions of stolen credentials against login forms. And yet, these bots are no longer only targeting high-value goods and accounts but hijacking and selling streaming and food delivery accounts.
The Four Industries Most Vulnerable to Bot Attacks
At Netacea, we wanted to know just how aware businesses are of bots and if they fully understand the threat to their businesses. Which roles are responsible, how confident are they in their bot mitigation strategies, and how well-placed is this confidence? We surveyed 200 enterprise businesses across travel, entertainment (including online gaming and streaming), e-commerce and financial services to get a broad picture of how bots are understood and protected against.
Cloud Threats Memo: Adding to the List of Exploited Cloud Services
Hosting phishing pages or malicious payloads on legitimate cloud services is now a consolidated modus operandi for bad actors.
DLP Can Be So Much More Than Compliance
When you think about your DLP approach, what immediately comes to mind? Is it primarily centered around compliance? Is it simply using vendor-provided patterns of interest to satisfy an industry-specific framework like PCI, PII, or GDPR? Chances are, this probably describes at least some part of your DLP strategy because it is not difficult to set up and can satisfy a key business requirement of regulatory compliance reporting.