LimaCharlie + @claude Code: Admin Tasks, MITRE Coverage, and EDR Detections [Demo]
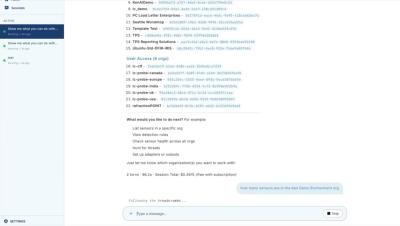
Claude Code runs directly inside the LimaCharlie UI, connecting to the MCP server and loading the skills needed to execute commands across your environment. In this video, you'll see it in action for common administrative tasks: identifying organizations and their IDs, pulling sensor counts for a specific org, and getting a full breakdown of containers by type. SOC managers can query this information conversationally rather than navigating multiple menus or writing custom scripts.