Unveiling Intrusions: Corelight NDR and CrowdStrike EDR in Action
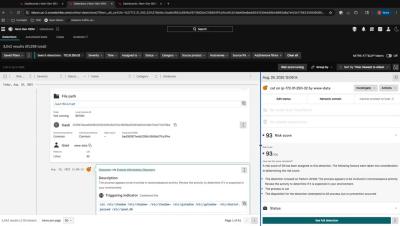
Adversaries are deliberately attacking devices that are difficult to monitor with EDR. In this video, you’ll see how you can use Corelight’s Network Detection & Response (NDR) inside of CrowdStrike Falcon to paint the full picture of an intrusion. NDR gives defenders the visibility they need to find intrusions on unmanaged devices of any type.