Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
What is the DevSecOps Maturity Model (DSOMM)?
7 DevSecOps Principals Every Developer Must Know
6 Essentials for a Near Perfect Cyber Threat Intelligence Framework
9 Top Cloud Threat Detection (CTR) Tools
What is DSPM (Data Security Posture Management) & Do You Need It?
Knowledge is power. Power is money. In the context of information systems and applications, knowledge is ingested, processed, and used as data. Data theft or loss can be devastatingly costly to a business. Data is one of an organization’s most valuable assets, and must be secured and protected as such.
Cloud Risk Management: The DevOps Guide
For DevOps software developers, navigating the cloud landscape without a clear understanding of risks is equivalent to walking into a minefield blindfolded. Cloud risk management, therefore, becomes an indispensable tool for DevOps – enabling us with the ability to identify, assess, and mitigate potential threats that could jeopardize their applications, their data, and their organization’s reputation.
Parallel Testing Unleashed: 10 Tips to Turbocharge Your DevOps Pipeline
Every software team is constantly looking for ways to increase their velocity. DevOps has emerged as a leading methodology that combines software development and IT operations to shorten the system development life cycle and provide continuous delivery. However, ensuring software quality and security in a high-velocity environment can be challenging. This is where parallel testing comes into play.
Top 10 Fraud Detection Solutions for 2024
It’s natural to want to believe that every new account creation or online purchase signals the legitimate growth of your business. But the alarming rise in financial and data losses attributed to fraud, suggests a different reality. There are thousands of bad actors actively looking to nickel and dime businesses and consumers. In 2022, a staggering 2.4 million fraud reports flooded the Consumer Sentinel Record.
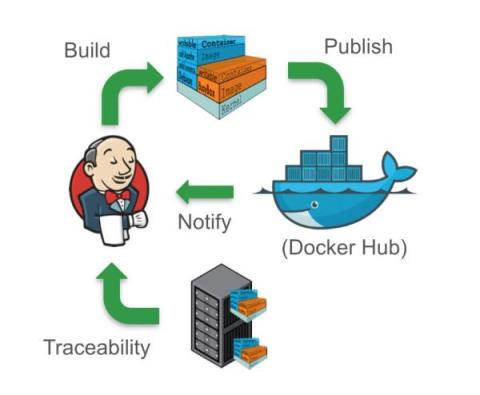
Mastering The DevOps Toolchain: 10 Essential to Build a DevOps Assembly Line
DevOps is more than just a buzzword and the dev behind the magic is more than just a tech wizard who orchestrates software delivery single-handedly. Behind the curtains is an assembly line of toolchains that makes DevOps possible. 44% of DevOps teams use between 2-5 tools, with 41% using 6-10 tools. High-performing teams also tend to use more tools, resulting in faster deployment cycles and delivering multiple times a month.