Elastic Security evolves into the first and only AI-driven security analytics solution
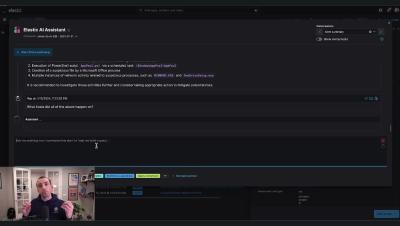
In our previous installation, we discussed the history of security information and event management (SIEM) solutions — from collection to organizational detections and finally to response and orchestration. Now, we are firmly in the SIEM 3.0 revolution and focused on applying generative AI to every applicable process in the security operations center with tremendous success.