Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
60 Second Charity Challenge: Password Managers
Harmonizing the Federal Effort on Automating Software Bill of Materials
When the Biden administration released Executive Order 14028, “Improving the Nation's Cybersecurity”, it included guidance to enhance the security of the nation’s software supply chain. As a result, key building blocks are being developed to both strengthen software security and bolster software Supply Chain Risk Management (SCRM) programs across the Federal government.
Introduction to Splunk Common Information Model
AppLocker Rules as Defense Evasion: Complete Analysis
Microsoft continues to develop, update and improve features to monitor and prevent the execution of malicious code on the Windows opearting system. One of these features is AppLocker. This feature advances the functionality of software restriction policies and enables administrators to create rules to allow or deny applications from running based on their unique identities (e.g., files) and to specify which users or groups can run those applications.
Introducing the Ransomware Content Browser
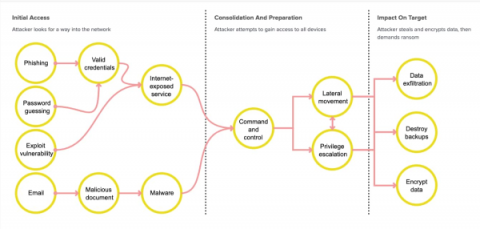
Splunk SURGe recently released a whitepaper, blog and video that outline the encryption speeds of 10 different ransomware families. The outcome of this research was that it is unlikely that a defender will be able to do anything once the encryption has started. Ransomware today is also mostly “human-operated” where many systems are sought out and compromised before any encryption activities occur and, once they do, the encryption is just too fast to meaningfully affect the damage done.
Coffee Talk with SURGe: Signal Numbers Exposed, FTC Data Privacy Rules, Conti Ransomware, E2EE
Coffee Talk with SURGe: 2022-AUG-10 Live from Black Hat:
Using Threat Intelligence To Advance Your Security Posture
People often ask me, “What’s the purpose of cybersecurity?” I tell them that it serves to protect the valuable, intangible data assets of firms or private individuals, usually by trying to shrink the attack surface. One way to achieve cybersecurity is to utilize threat intelligence research in your firm’s security plan. In this article, I will discuss the benefits of understanding and implementing a threat intelligence program.
Cyberattacks in 2022: Beware These 5 Attack Types
Cyberattacks are constantly changing. That you know. But how are they changing? And which types of threats are the most prominent today? Those are the real questions you need to answer to stay ahead of modern security risks. Keep reading for a primer on the most prevalent types of cyber security threats in 2022, along with insights on how to build a defense strategy against them. (For a comprehensive view, check out our cybersecurity threats explainer.)
Splunk Announces Participation in the Open Cybersecurity Schema Framework (OCSF) Project
There’s a myth from antiquity known as the Tower of Babel, where people were working together to build a tower to the heavens, only to lose the ability to communicate with one another via divine intervention. Essentially, the groups began speaking their own languages and were unable to complete the tower. So, why are we talking about myths in a cybersecurity blog?
The Democratization of Data: The Pros & Cons of All That Data
Try going one day without navigating today’s data landscape — accepting or declining cookie pop-ups, determining whether and how a company can use your information, and all the data you’re generating simply by browsing the web. Yes, we live in the Data Age. We know we generate mind-boggling amounts of data. The data we generate in a single day is an unfathomable amount (2.5 quintillion bytes if you can do that math). More formally, we say that data has been democratized.
Security Made Stronger with Splunk User Behavior Analytics (UBA) Version 5.1
The Summer of Security continues! Hot on the heels of security announcements at.conf22 and a brand new Splunk Security Essentials 3.6.0, we’re excited to announce the availability of User Behavior Analytics (UBA) version 5.1.
The Convergence of Security and Observability: Top 5 Platform Principles
With the advances in technology and an unpredictable macro environment, IT professionals have to deal with a deluge of data, increasing cyberthreats, distributed infrastructure and workforce, a mix of modern and monolithic apps and hybrid environments. Although there is significant momentum towards the Cloud, many organizations cannot move all of their data to the public cloud due to security, compliance or technical constraints.