SessionReaper (CVE-2025-54236): Impact, Detection, and Mitigation
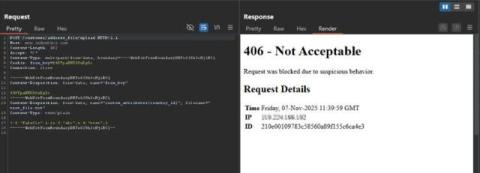
SessionReaper (CVE-2025-54236), an unauthenticated vulnerability in the Commerce REST API enables session takeover and possible RCE. If you run Adobe Commerce or Magento Open Source, this critical, pre-auth vulnerabilities can let attackers hijack customer accounts, manipulate orders, and in many real-world setups drop persistent PHP web shells on your servers.