Security Bulletin: ClickFix and the New Era of Social Engineering
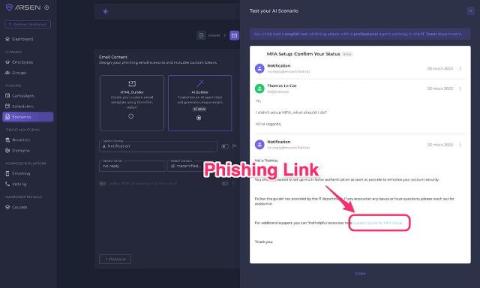
ClickFix is an emerging social engineering technique that has gained traction among both cybercriminals and APT groups due to its effectiveness and low barrier to execution. First observed around October 19, 2023, disguised as Cloudflare anti-bot protection, ClickFix deceives users into taking action to “fix” a non-existent issue, often through fake reCAPTCHA pages, spoofed software updates, or fraudulent security prompts.