Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
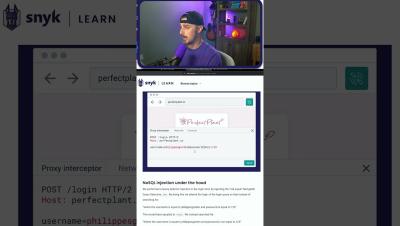
Exploit Attempt for a Cross Site Scripting Vulnerability
Watch the full video for more...
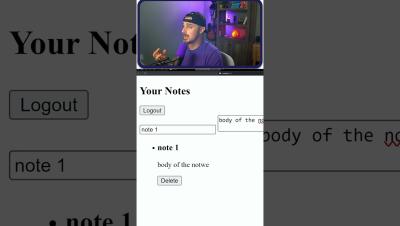
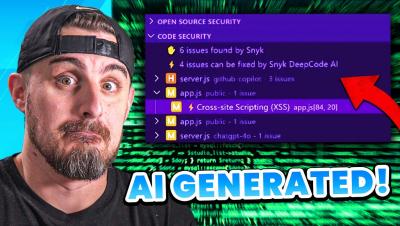
Exploiting AI Generated Code
If you are using AI coding assistant tools, you need to be cautions when doing so, as these tools often generate code with vulnerabilities. In today's video we will be attempting to exploit two vulnerabilities that were found in AI generated code, as well as showing you how you can easily fix them.
Can AI Build a Secure App? Part 1
Watch the full video for more and for part 2...
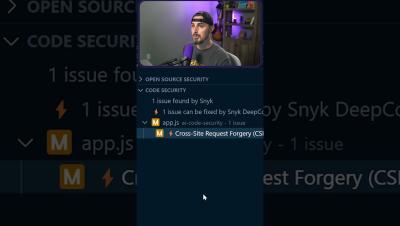
How AI Almost Got Me FIRED: Part 4
AI got me fired AGAIN?!...Just kidding! In this video, we are using the AI tools ChatGPT and Perplexity.ai to help us with coding. We will also be taking a look at how you can identify and fix any vulnerabilities that these tools may generate.
Why ASPM is the Future of AppSec
ASPM (Application Security Posture Management) is the future of application security. It provides a centralized dashboard that gives security teams visibility into application assets and their relationships. ASPM also prioritizes risk based on context so you can focus on the vulnerabilities that matter most. This video will explore the challenges facing security teams today and how ASPM can help you overcome them.