Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Empowering Small Businesses Through Effective Time Tracking
The Two Sides of ChatGPT: Helping MDR Detect Blind Spots While Bolstering the Phishing Threat
ChatGPT is proving to be something of a double-edged sword when it comes to cybersecurity. Threat actors employ it to craft realistic phishing emails more quickly, while white hats use large language models (LLMs) like ChatGPT to help gather intelligence, sift through logs, and more. The trouble is it takes significant know-how for a security team to use ChatGPT to good effect, while it takes just a few semi-knowledgeable hackers to craft ever more realistic phishing emails.
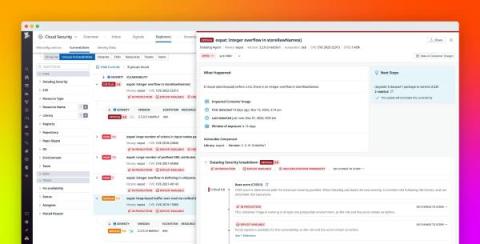
Mitigate infrastructure vulnerabilities with Datadog Cloud Security Management
Cloud environments comprise hundreds of thousands of individual components, from infrastructure-level containers and hosts to access-level user and cloud accounts. With this level of complexity, continuous and end-to-end visibility into your environment is vital for detecting, prioritizing, and fixing vulnerabilities before attackers can take advantage of them.
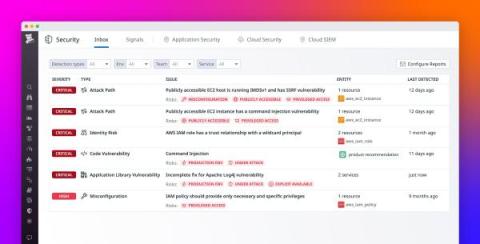
Easily identify and prioritize your top security risks with Datadog Security Inbox
In today’s complex cloud environments, security and engineering teams need to manage vulnerabilities and misconfigurations across multiple layers of the stack, including cloud resources, clusters, containers, and applications. Often, this results in a lengthy list of problems that lacks prioritization and is daunting for users to address.
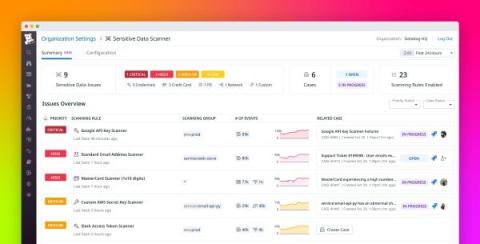
Discover, triage, and remediate sensitive data issues at scale with Sensitive Data Scanner
Managing sensitive information in your telemetry data poses many challenges to governance, risk management, and compliance (GRC) teams and overall security. Organizations in healthcare, finance, insurance, and other fields must carefully adhere to strict compliance requirements. But sensitive data comes in many forms and moves between many endpoints, and as a result, it can easily become exposed in telemetry data.
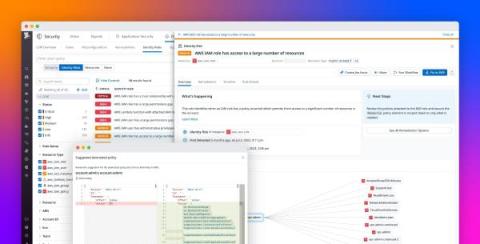
Find and remediate identity risks with Datadog CIEM
Identity and access management (IAM) systems are necessary for authenticating and authorizing access to your environment. However, their mismanagement is one of the leading causes of breaches and insider threats today. Engineering teams must rapidly provision identities and permissions to keep pace with infrastructure growth—consequently, the ratio of non-human or machine identities to every human identity is also increasing at a substantial rate.
Making the cloud the safest place to compute: Sumo Logic Cloud Infrastructure Security for AWS
Black Friday: Loved by Shoppers and Fraudsters Alike
For some, Black Friday conjures images of parasite-infected shoppers running amok in a mall. (Rotten Tomatoes gives the movie a 65% rating). For bargain hunters, it is a whirlwind of unbeatable deals and frenzied shopping sprees. Thanksgiving Day, Black Friday and Cyber Monday are the year’s biggest days for American merchants. The hype has crossed borders.
Fuzzer-V
An overview of a fuzzing project targeting the Hyper-V VSPs using Intel Processor Trace (IPT) for code coverage guided fuzzing, built upon WinAFL, winipt, HAFL1, and Microsoft’s IPT.sys.