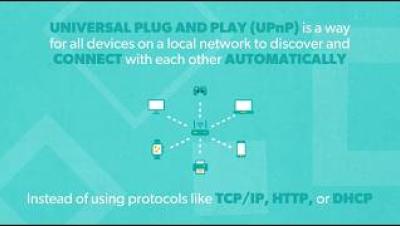
What is UPnP? And Why is it Still a Security Risk?
In this video, learn what UPnP is, what it does, use cases, why it's a security risk, and security measures you can take. Learn more about: Resources and social media: Transcript: Universal Plug and Play, or UPnP, is a way for all devices on a local network to discover and connect with each other automatically, rather than having to connect each device by manually entering protocols like TCP/IP, HTTP, or DHCP.