Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Exploring Endpoint Security: From Basics to AI-Era Threats, With Raakesh Thayyil
From antivirus to AI-powered threats, this session with Raakesh Thayyil (Group Head of Security & Privacy at PropertyGuru) breaks down the evolving world of endpoint security—what it means today, how remote work changed the game, and what lean security teams can actually do about it. What you’ll learn: Timestamps & Q&A included in the video chapters! Brought to you by The 403 Circle – an invite-only community for top CTOs & CISOs.
MFA Bypass Risks: What You Need to Know in 2025
In Uber’s 2022 breach, attackers didn’t crack encryption or exploit some unknown flaw. They flooded an employee with MFA prompts until they became exhausted. One careless tap, and an entire enterprise was open. The lesson isn’t that MFA failed. It’s that MFA itself can become the exploit surface. From AiTM phishing proxies like EvilGinx to automated OTP interception, attackers treat MFA like DevOps treats CI/CD, i.e, scalable, repeatable, and scriptable.
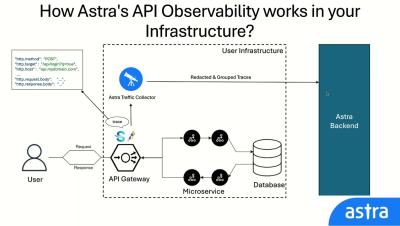
Introducing Astra API Security Platform - Discover, Scan & Secure Your APIs
Astra API Security Platform is a tool purpose-built to help security-conscious teams find, classify, and secure every API they own. Shadow, dormant, undocumented. Auto-discovers every API in the environment with real-time traffic analysis and continuously scans them with 15,000+ test cases, no guesswork required. What You Can Do with Astra API Security Platform: Enable continuous pentest at scale with Astra.
How Effective Is 'Shift-Left Security' for Protecting APIs?
Your API rollout is on track. Code’s tested, endpoints documented. John from security asks for the third revision of your vulnerability assessment, and your release date slips another two weeks. Sounds familiar? You are not alone. According to a recent report by Salt Security, 99% companies reported at least one API security incident in 2024-25. And here’s the kicker: 95% API attacks come from authenticated sessions, proving that tokens alone don’t cut it anymore.
Get started with Astra API Security platform with Observability
In this video, we’ll walk you through how to get started with the Astra API Security Platform, now enhanced with Observability features. You’ll learn how to: Whether you’re a developer, security engineer, or product leader, this guide will help you quickly set up Astra and gain complete visibility into your API security.
Top 10 Penetration Testing Companies UK
In the first half of 2024, 7.78M attacks hit the UK, driven by AI-fueled threats and persistent exposure. Even with Zero-Trust, human error and zero days can still risk an AI-powered breach. Penetration testing is crucial but with 50+ providers, who can you trust?
How Often Are VMs Scanned in Azure CSPM?
Azure CSPM (Cloud Security Posture Management) helps users maintain secure cloud setups. This post covers the basics, including the role of scanning virtual machines, various scan methods, and methods for viewing results.
How to Use the OWASP AI Testing Guide to Pentest AI Applications (2025)
For years, the cybersecurity community has discussed the theoretical risks of artificial intelligence. We’ve imagined biased algorithms and adversarial attacks, but these conversations usually stayed hypothetical. That era is over. It’s time to move beyond the theory and into the practical “how-to” of finding and exploiting vulnerabilities in AI systems. To execute this, the new OWASP AI Testing Guide (AITG) is indispensable.
Practical Guide to Integrating DAST in Your DevOps Workflow (2025)
Globally, DDoS attacks surged 108% year‑over‑year, API‑targeted bot assaults jumped 39%, and nine out of ten sites faced bot attacks by the end of 2024. Application‑layer threats are evolving faster than ever, and annual or quarterly scans simply can’t keep up. Yet most teams still treat security as a checkbox, i.e., formal, slow, and disconnected from rapid releases.