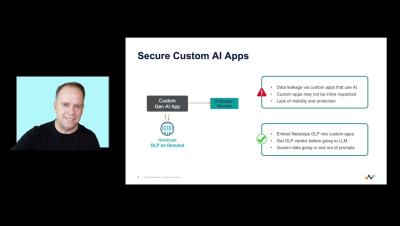
Demo - Netskope DLP on Demand
Netskope DLP on Demand extends the power of Netskope DLP virtually anywhere. This is accomplished by providing an API abstraction of Netskope DLP enabling any application of service to utilize Netskope DLP for inspection of data for visibility and protection.