Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Log4j/Log4Shell One Year Later: Endemic Vulnerability Indeed
On December 9, 2021, Apache upended the cybersecurity industry by publishing a zero-day vulnerability (CVE-2021-44228) for its ubiquitous Log4j logging utility. Dubbed Log4Shell, the remote code execution flaw (CVSS score:10) allows an attacker to take control of a connected device and run malicious code, access sensitive data or alter its configuration. Because Logj4 is free and easy-to-use, it’s embedded (often deeply) in Java applications used by IT and OT platforms worldwide.
SBOMs and the Hunt for Software Supply Chain Vulnerabilities
That’s an excerpt from the fact sheet accompanying the May 2021 Executive Order on Improving the Nation’s Cybersecurity (EO). It refers to one of seven ambitious measures in the EO: shoring up security of that notorious playground for hackers, the software supply chain. Knowing that organizations lack visibility into the components that comprise their connected assets, bad actors can have a field day exploiting vulnerabilities to penetrate networks and take control.
What Project Memoria Foretold about TCP/IP Security and Supply Chain Vulnerabilities
Project Memoria was the largest study about the security of TCP/IP stacks, conducted by Vedere Labs and partners in the cybersecurity industry. It started from a collaboration with JSOF to understand the impact of Ripple20 and led to the discovery of almost 100 vulnerabilities in 14 TCP/IP stacks, divided into five phases: AMNESIA:33, NUMBER:JACK, NAME:WRECK, INFRA:HALT and NUCLEUS:13.
The Increasing Threat Posed by Hacktivist Attacks: An Analysis of Targeted Organizations, Devices and TTPs
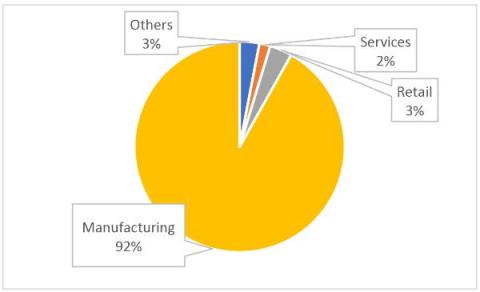
This year has seen an enormous increase in the number and claimed impact of hacktivist attacks on critical infrastructure and enterprises operating in critical services. Many attacks target unmanaged devices such as Internet of Things (IoT) and operational technology (OT) equipment. Attacks are motivated by geopolitical or social developments across the globe, with the goal of spreading a message or causing physical disruption.
OT:ICEFALL Continues: Vedere Labs Discloses Three New Vulnerabilities Affecting OT Products - How to Mitigate
Continuing our OT:ICEFALL research, Vedere Labs has disclosed three new vulnerabilities affecting OT products from two German vendors: Festo automation controllers and the CODESYS runtime, which is used by hundreds of device manufacturers in different industrial sectors, including Festo.
Extend Your SOC Team with 24/7 Remote OT Security
Some economic sectors may be hitting the brakes, but the cybersecurity talent shortage persists across all industries and shows no signs of abating – not while sophisticated cyberattacks continue to rise in number and complexity. The 2022 (ISC)2 Cybersecurity Workforce Study found that even as the global cybersecurity workforce is at an all-time high, it is still short by 3.4 million workers.
Vulnerability vs. Threat vs. Risk vs... "Other"
In cybersecurity, three key terms are vulnerability, threat and risk. Often they’re tossed around interchangeably, but they have a specific relationship to one another..
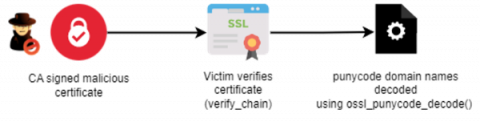
OpenSSL CVE-2022-3602 and CVE-2022-3786 (Spooky SSL): What They Are and How to Mitigate Risk
On November 1, OpenSSL v3.0.7 was released, patching two new high-severity vulnerabilities: CVE-2022-3602 and CVE-2022-3786. The new vulnerabilities have been dubbed by the community as “Spooky SSL,” although the name is not recognized by the OpenSSL team. CVE-2022-3602 was originally discovered by a researcher known as Polar Bear, while CVE-2022-3786 was found during the analysis of the first vulnerability by Viktor Dukhovni.
Company Update: Forescout Enters Its Next Phase of Evolution
Over the last two years since going private, Forescout has undergone a significant transformation. We are extremely proud of our 20+ year heritage as the world’s leading network access control provider, yet we knew that we had untapped potential.