|
By Zoe Hawkins
In November 2023, Sumo Logic experienced a security incident. While no one wants to be a victim of a cyberattack, and we certainly learned a lot about things that we can do better in the future, our team was lauded by customers and media alike for how we handled the situation underscoring the importance of a good incident response plan. One of the core values at Sumo Logic is that we’re in it with our customers. But more broadly speaking, we’re in it with the InfoSec community.
|
By Christopher Beier
The power of artificial intelligence (AI) and machine learning (ML) is a double-edged sword — empowering cybercriminals and cybersecurity professionals alike. AI, particularly generative AI’s ability to automate tasks, extract information from vast amounts of data, and generate communications and media indistinguishable from the real thing, can all be used to enhance cyberattacks and campaigns.
|
By Anton Ovrutsky
It seems as though responders cannot catch a break when it comes to 0-day vulnerabilities and supply chain compromise avenues. On March 29th, 2024, the Cybersecurity & Infrastructure Security Agency published an alert regarding a supply chain compromise of the XZ Utils package. At time of writing, there is no information regarding exploitation of the vulnerability and follow-on post-compromise activity.
|
By Anton Ovrutsky
In today’s cloud-native world, systems are usually accessed by users from multiple devices and in various geographic locations. Anyone who has tried to operationalize an impossible travel type alert for cloud resources will understand the myriad nuances and gotchas involved in such an endeavor. A user may be accessing a cloud resource from a mobile device that is tied to a carrier network well away from their normal geographic location.
|
By Chas Clawson
Imagine needing to stop a playoff game because viewers were actively impacting the sport, helping players catch impossible passes or score points they never should have gotten. That’s the equivalent of what happened when an Apex Legends hack during the North American finals interrupted the tournament and raised cybersecurity concerns for everyone involved. With global esports a billion-dollar industry, and competitive video gaming in general worth much more than that, this has a serious impact.
|
By Joe Kim
We’ve been talking about digital transformation for years (or even decades?), but the pace of evolution is now being catapulted forward by AI. This rapid change and innovation creates and relies upon exponential data sets. And while technology is rapidly evolving to manage and maintain these massive data sets, legacy pricing models based on data ingest volume are lagging behind, making it economically unsustainable.
We recently spoke to a focus group of security professionals, software engineers and developers for a discussion on DevSecOps. We’ve quoted a few of them throughout this article.
|
By Sumo Logic
Data protection principles are the same whether your data sits in a traditional on-premises data center or a cloud environment. However, the way you apply those principles is quite different when it comes to cloud security vs. traditional security. Moving data to the cloud – whether it's a public cloud like AWS, a private cloud or hybrid cloud — introduces new attack surfaces, threats and challenges, so you need to approach security in a new way.
|
By Dario Forte
It seems that “no-code” is a term we hear more often in the security automation context these days. And this is especially true because automation has become one of the major talking points in cybersecurity. How is no-code automation implemented in cybersecurity? How do no-code and Sumo Logic automation compare to each other? We’ll discuss all these questions in the following sections.
|
By Anton Ovrutsky
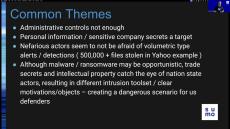
Today’s cyber threat landscape necessitates that we, as defenders of the enterprise, place identities at the center of our detection, prevention and response efforts. Indeed, threat actor tactics and techniques observed in the wild demonstrate that credential theft presents a large risk to the confidentiality, integrity and availability of our systems - be they on premises or in the cloud.
|
By Sumo Logic
Join Sumo Logic's Seth Williams, Field CTO, Channels and a stellar lineup of partners to discuss key trends and challenges today's MSSPs are tackling.
|
By Sumo Logic
It’s no secret threat actors, and cloud attacks have evolved, yet traditional security responses have languished, much to the detriment of many organizations. In this session, Cas Clawson, Field CTO for Security at Sumo Logic, will explore cloud threat detection challenges and how to do it better using a real-world incident response example, leveraging a single source of truth, breaking down team silos, and utilizing the best practices with DevSecOps.
|
By Sumo Logic
The 5th generation of SIEM is here. One where AI takes center stage. In this session, Steve Stover, VP of Product Management at Sumo Logic, will talk about the four core attributes of 5th-generation SIEM solutions, how AI impacts the seven stages of the cyber kill chain, and how organizations can use AI to defend themselves.
|
By Sumo Logic
In today's rapidly evolving landscape of cybersecurity, the integration of artificial intelligence (AI) presents both unprecedented opportunities and complex challenges. Understanding the implications of AI in modern defense strategies is paramount for organizations seeking to safeguard their digital assets against emerging threats. In this Q&A, Chas Clawson, Sumo Logic's Field CTO, Security, shares insights on defending against AI-enabled adversaries and how to integrate AI-driven technologies into security strategies and frameworks.
|
By Sumo Logic
Get the highlights from Day 1 of RSA and learn all about how Sumo Logic helps unify DevSecOps with a single source of truth through enterprise-class threat detection, AI-driven alerting, and real-time threat intelligence.
|
By Sumo Logic
In this session, Anton and Paul cover how to detect unknown and insider threats along with a discussion of User-Entity Behavior Analytics (UEBA) using Sumo Logic's Cloud SIEM.
|
By Sumo Logic
Join us as Chas and Christopher teach how Sumo Logic Cloud SIEM helps with TDIR.
|
By Sumo Logic
Together, Gigamon and Sumo Logic enable organizations to build an effective and efficient monitoring and security posture. Matt Rosenbaum, Partner Architect at Sumo Logic and Stephen Goudreault, Cloud Security Evangelist from Gigamon cover three top Security Use Cases for this integration. Security Posture Suspicious Activities Rogue Activities As premier AWS partners, you can find both Sumo Logic and Gigamon in the AWS Marketplace.
|
By Sumo Logic
Sumo Logic Cloud SIEM helps teams broaden threat visibility across the entire enterprise. With uniformity, clarity and transparency, companies can bring all their security tools together for complete visibility. Cloud SIEM automates real-time threat investigation, incident management and threat response while reducing false positives and analyst fatigue. Bring your teams together with centralized data and cloud-native scale in a SaaS Log Analytics Platform that breaks down silos.
|
By Sumo Logic
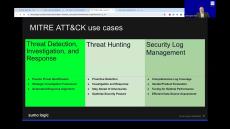
Please join us as Christopher and Melissa as they teach us about Sumo Logic's MITRE ATT&CK Coverage Explorer!
|
By Sumo Logic
Security information and event management (SIEM) solutions have been around since 2000, and they were developed with the goal of helping organizations in the early detection of targeted attacks and data breaches.
|
By Sumo Logic
SIEM stands for Security Information and Event Management and these solutions have been around since 2000. They were developed with the goal of helping organizations in the early detection of targeted attacks and data breaches.
|
By Sumo Logic
In this paper we will discuss some of the general philosophies and perspectives that will assist anyone who wants to securely leverage the benefits the cloud by using its strengths to overcome issues that have traditionally been labeled as weaknesses.
|
By Sumo Logic
This white paper describes the technologies and processes used by Sumo Logic to secure customer data, and provides background on the company's deeply ingrained security culture.
|
By Sumo Logic
This white paper is intended to support stakeholders movement of applications to the cloud, and provide some fundamental approaches to adopt in order to better protect every layer of the AWS infrastructure.
- May 2024 (5)
- April 2024 (4)
- March 2024 (4)
- February 2024 (2)
- January 2024 (5)
- December 2023 (1)
- November 2023 (8)
- October 2023 (6)
- September 2023 (7)
- August 2023 (6)
- July 2023 (5)
- June 2023 (5)
- May 2023 (14)
- April 2023 (6)
- March 2023 (2)
- February 2023 (3)
- January 2023 (3)
- December 2022 (4)
- November 2022 (5)
- October 2022 (3)
- September 2022 (13)
- August 2022 (1)
- July 2022 (3)
- June 2022 (5)
- May 2022 (2)
- April 2022 (4)
- March 2022 (4)
- February 2022 (3)
- January 2022 (5)
- December 2021 (5)
- November 2021 (4)
- October 2021 (8)
- September 2021 (18)
- August 2021 (14)
- July 2021 (11)
- June 2021 (6)
- May 2021 (2)
- April 2021 (2)
- March 2021 (3)
- February 2021 (2)
- January 2021 (5)
- December 2020 (8)
- November 2020 (1)
- October 2020 (4)
- September 2020 (1)
- August 2020 (1)
- July 2020 (8)
- June 2020 (7)
- May 2020 (7)
- April 2020 (4)
- March 2020 (6)
- February 2020 (5)
- January 2020 (2)
- December 2019 (2)
- November 2019 (1)
- October 2019 (7)
- September 2019 (5)
- August 2019 (6)
- July 2019 (3)
- June 2019 (5)
- May 2019 (2)
- April 2019 (2)
- March 2019 (4)
- February 2019 (3)
- January 2019 (2)
- November 2018 (2)
- October 2018 (1)
- July 2018 (1)
- June 2018 (1)
Empowering the People Who Power Modern Business. A Cloud-native Machine Data Analytics Platform for DevSecOps.
Sumo Logic is a secure, cloud-native, machine data analytics service, delivering real-time, continuous intelligence from structured, semi-structured and unstructured data across the entire application lifecycle and stack.
Build, run and secure your AWS, Azure, Google Cloud Platform or Hybrid applications with Sumo Logic, a cloud-native, machine data analytics service for log management and time series metrics.
- Optimize Continuous Delivery: Accelerate development, testing, & deployment of your application.
- Monitor & Troubleshoot in Real Time: Enable DevOps to proactively identify and fix performance issues.
- Secure Your Platform: Detect, investigate and respond to security issues instantly.
- Simplify Compliance Management: Ensure compliance with HIPAA, PCI, GDPR and much more.
One platform for real-time, Continuous Intelligence.