External Exposure & Attack Surface Management For Dummies
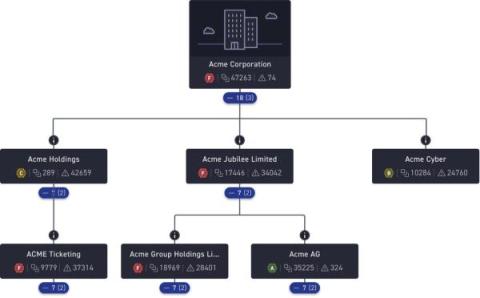
Your attack surface has grown, it's now in cloud infrastructure and across subsidiaries and unknown, unmanaged assets are everywhere. How are you finding these? Attackers look for, find and attack these unknown assets and when there are externally exposed risks, sensitive data and critical systems are put in danger. Read now, External Exposure & Attack Surface Management For Dummies.