Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Zero Trust isn't a Buzzword
Achieving Zero Trust? One Size Does Not Fit All
More than a year of near-universal remote work has proven that many of us can reliably stay productive from anywhere — whether it be from home, co-working spaces or otherwise. Businesses have caught wind of this, and according to IDC, 60% of them will continue with remote work or implement a hybrid model even after they reopen their offices again. This calls for a paradigm shift in the way we conduct cybersecurity.
A buyers guide: What to consider when assessing a CASB with Hank Schless
Cloud Applications: A Zero Trust Approach To Security For Healthcare
Lookout CASB Named a Major Player in 2021 IDC MarketScape Cloud Security Gateways
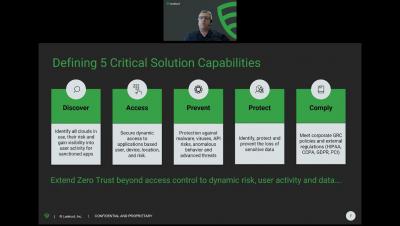
I am excited to share a major milestone for our company: the Lookout Cloud Access Security Broker (CASB) has been named a Major Player in the 2021 IDC MarketScape Worldwide Cloud Security Gateways (CSG) Vendor Assessment (Doc # US48334521, November 2021). When Lookout acquired CipherCloud back in March 2021, the two companies came together with a mission to build a platform that provides intelligent Zero Trust access by leveraging in-depth telemetry from endpoint to cloud.
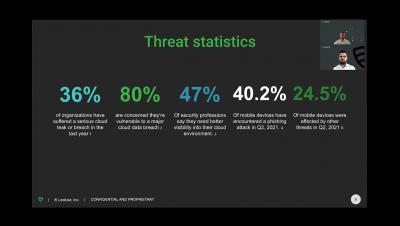
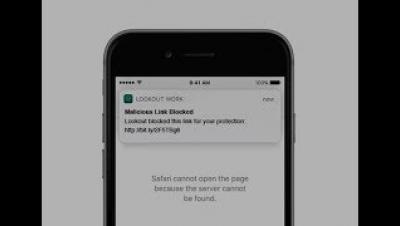
Mobile Phishing: A massive threat on a small screen
Our SASE Journey: Lookout Head of IT Talks Shop
Like other organizations that are adopting a permanent hybrid or remote-first work environment, Lookout is using our Secure Access Services Edge (SASE) platform to implement cybersecurity that is not tied to the physical office spaces where employees used to work. SASE is a security framework defined by Gartner that has been adopted by many organizations to enable intelligent Zero-Trust access from anywhere without hindering productivity.