10 essential cybersecurity tips for beginners
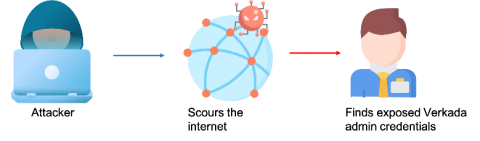
Organizations today are challenged by an increased exposure to cyber threats. Attackers often target emerging technologies since the new technology is often ill-equipped to handle an attack. Moreover, the internet has become filled with malicious links, Trojans, and viruses.