Advanced Data Tokenization: Best Practices & Trends 2025
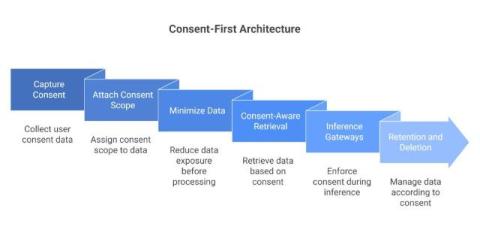
Breaches got faster. Architectures got messier. And data stopped living in tidy tables. Modern stacks push personal and regulated data through microservices, data lakes, event streams, vector stores, and LLM prompts. Encryption still matters, but it protects containers, not behaviors. As soon as an app decrypts a record, risk comes roaring back.