Hackers Skipped the Payment Step: BLA 4 is Pure Logic Evasion #transitionvalidation #businesslogic
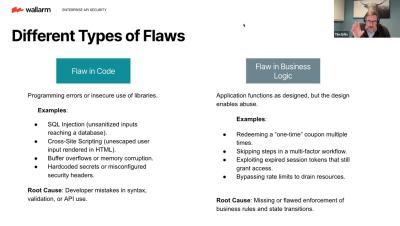
Missing Transition Validation (BLA 4) is a subtle but devastating threat. It exploits the sequence of steps in your application's workflow. The flaw? Your application fails to check that Step 2 (Payment) occurred before allowing access to Step 3 (Confirmation). The attacker simply draws a line straight to the goal! This attack is: Difficult to Detect: It uses valid requests in an invalid sequence. Tightly Coupled: It's unique to your application's specific logic. You need deep, sequence-aware runtime protection.