SpringShell (Spring4Shell) Zero-Day Vulnerability CVE-2022-22965 : All You Need To Know
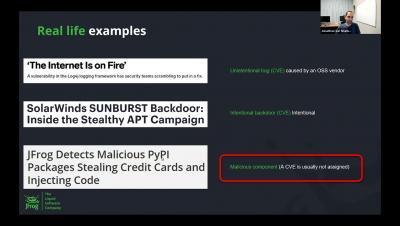
On March 29th, the cyberkendra security blog posted a sensational post about a Log4Shell-equivalent zero-day vulnerability in Spring Framework, but without any solid details about the vulnerability itself.