Detect Multi-Stage Threats with Behavioural Detections in Falcon Next-Gen SIEM
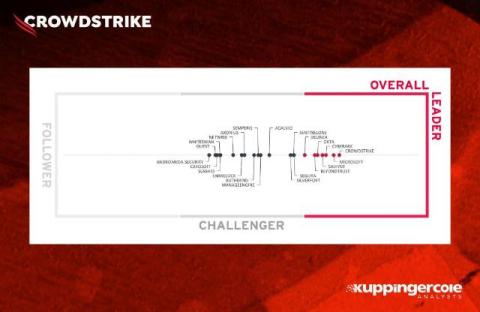
See how Falcon Next-Gen SIEM uses Behavioural Detections to expose complex, multi-stage attacks that static rules miss. Watch how security teams correlate related events across all data—endpoint, cloud, and third-party—to detect stealthy threats in real time and respond with confidence. CrowdStrike Falcon Next-Gen SIEM: Consolidate security operations with the world’s most complete AI-native SOC platform.