Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
How to Fuzz Java with CI Fuzz CLI
All software has bugs, and some can be difficult to find or reproduce. However, not all approaches to bug-finding need to be difficult to use! Fuzzing is an undeniably effective approach to finding security issues and bugs in software projects, however, tools can be complex to set up and execute. CI Fuzz CLI (open-source), automates the parts that make fuzzing complex, giving its users the look and feel of a unit test.
Uncovering Hidden Bugs and Vulnerabilities in C/C++ | How to Fuzz Your Code With 3 Commands
Code Intelligence Unveils Simple Open-Source Tool to Automatically Test Java Applications for Unexpected Behaviors
Build Secure Java Applications with Fuzz Testing
Today, I want to show you a way how to increase the integrity and functionality of your Java applications, with fuzz testing. This awesome testing approach has done me great service for building more secure Java applications, and it's basically as simple as unit testing. In this article, I will share how you can apply fuzz testing to your own code. And the best part: all code examples and tools I will use are 100% open-source.
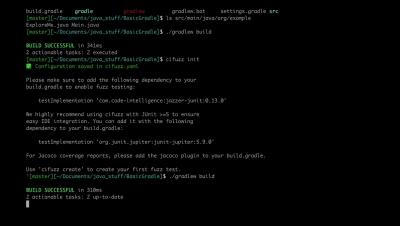
Fuzzing Java Applications With CI Fuzz | Gradle
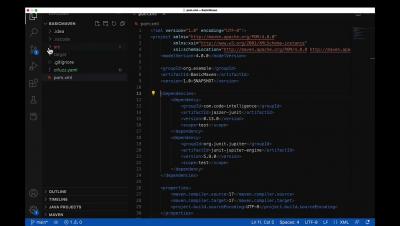
Fuzzing Java Applications With CI Fuzz | Maven
Mock Testing Embedded Systems With Fuzz Data
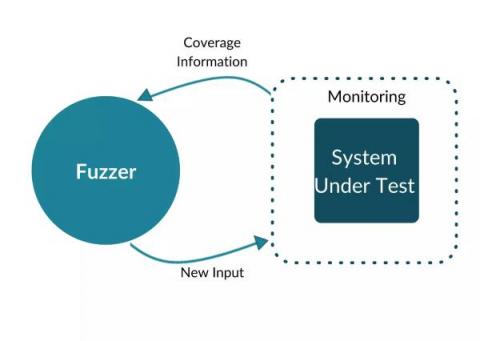
Mock testing, also called mocking, is an integral part of the embedded software development process as it allows you to test your code without relying on actual hardware. This can be extremely helpful when trying to debug your code or test new features. During fuzzing testing, applications are tested using unexpected or invalid inputs. Modern fuzzers generate these inputs based on feedback about the SUT’s interaction with previous test inputs.