Unsolved Challenge: Why API Access Control Vulnerabilities Remain a Major Security Risk
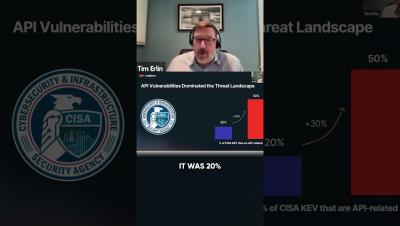
Despite advancements in API security, access control vulnerabilities, such as broken object-level authentication (BOLA) and broken function-level authentication (BFLA), remain almost impossible to detect. This blog will explore why these vulnerabilities are so difficult to detect, the limitations of current security tools, and the implications for businesses relying on API-driven applications. It will also discuss potential approaches for improving API security posture.