Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Cybersecurity for SMEs - applying a Data-centric lens
2021 SecureAge COVID & cybersecurity study
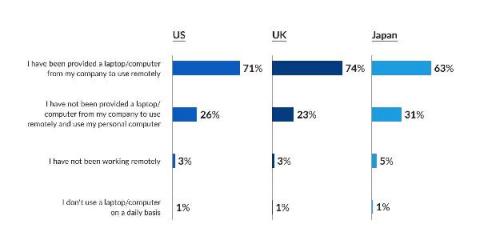
In 2021 SecureAge surveyed 1,000 US-based respondents (400+ employers; 600+ employees), 600 UK-based respondents (200+ employers; 400+ employees), and 300 Japan-based respondents (100+ employers; 200+ employees) to find out more about cybersecurity concerns during the pandemic and what has been done to prepare for the future. The study, conducted between July and August 2021, revealed new cybersecurity trends as well as how businesses have and have not adapted.
The biggest threat to modern society - and its not Covid
5G robots began their first scouts around Singapore’s luxury neighbourhood Keppel Bay last month - a trend that will spread globally in the years to come. These autonomous robots came in several forms, and were adapted specifically for a variety of duties that gave ground staff a chance to perform their duties via proxy, away from the hot tropical sun. This included monitoring water quality, garbage collection, and security surveillance.