Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
The Twistlock Acquisition: An Analysis of Palo Alto Networks' strategy
Congratulations Twistlock! One of the best signs of an emerging market is when existing, massive players are willing to put hundreds of millions of dollars on the line to get into that market right now. Given today’s Twistlock acquisition by Palo Alto Networks, and other recent acquisitions like Heptio/VMware, we believe this is happening in the cloud-native market. Congratulations to Twistlock on their success.
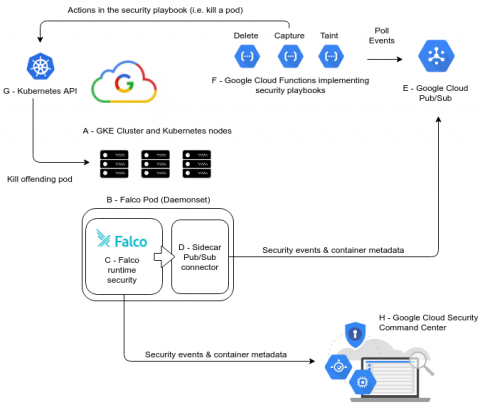
GKE security using Falco, Pub/Sub and Cloud Functions
In this blogpost we will demonstrate how to build a complete GKE security stack for anomaly detection and to prevent container runtime security threats. We will integrate Falco runtime security engine with Google Cloud Functions and Pub/Sub.
A Closer Look at Falco CVE-2019-8339
Recently, a member of the Falco community privately disclosed a capacity related vulnerability which, under circumstances where a malicious actor has already gained access to your system, could allow the actor to further bypass Falco’s detection of abnormal activity. The final details are still being worked out, but we believe the CVE will be classified as Medium severity according to the CVSS methodology.
Falco 0.15.0 Released
We are happy to announce the release of Falco 0.15.0. This release incorporates a number of improvements, as well as bug fixes, and rules updates. This release also includes a mitigation for CVE-2019-8339, and all users are encouraged to update to this release. You can find more details about the features and improvements in the release notes, but below are a few highlights.
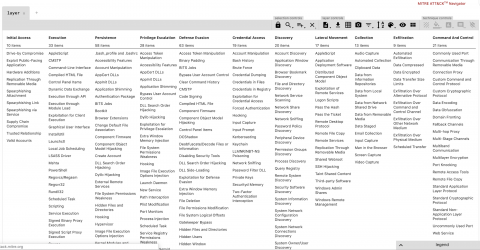
MITRE ATT&CK framework for container runtime security with Sysdig Falco
MITRE ATT&CK is a comprehensive knowledge base and complex framework of over 200 techniques that adversaries may use over the course of an attack. While MITRE’s full ATT&CK framework is publicly available, it can be characterized into 3 key elements.