Hiding in plain sight: HTTP request smuggling
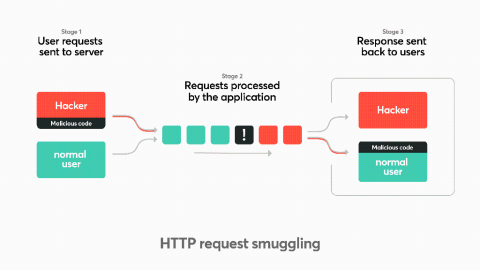
HTTP request smuggling is increasingly exploited by hackers in the wild and in bug bounty programs. This post will explain the HTTP request smuggling attack with remediation tips. HTTP request smuggling is an attack technique that abuses how two HTTP devices send requests between each other (typically a front-end proxy or a HTTP-enabled firewall and a backend server) or chaining multiple servers together with different configurations.