Phishing Kit Attacks Are Now Everywhere: How SOC Analysts Can Detect Them
Image Source: depositphotos.com
Phishing kits have changed the speed of compromise. Attackers no longer need malware or complex tooling. With ready-made phishing platforms, they can launch large-scale credential theft campaigns that bypass MFA and deliver valid sessions almost instantly.
By the time an alert reaches the SOC, the attacker may already be inside. Stopping these attacks now depends on seeing the full phishing chain early, before stolen access turns into business damage.
What Makes Phishkits Difficult to Catch?
Phishkit activity often appears normal until the account takeover is already in progress, leaving very little time to respond.
- Clean lures that pass email and web filters
- Reverse-proxy logins that look legitimate in authentication logs
- Fast-rotating domains that evade blocklists
- Valid sessions and cookies instead of brute-force behavior
- No malware at the first stage, so file-based detection misses it
- Minimal response window because attackers act within minutes
How Advanced SOC Teams Unpack Hybrid Phishkits in Minutes
Hybrid phishkits are raising the difficulty level because they’re no longer “one kit, one flow.” In blended chains, multiple kits work together, mixing infrastructure, redirects, and credential theft methods, which makes both detection and attribution messier.
View a real sandbox session of a Salty2FA + Tycoon2FA hybrid chain
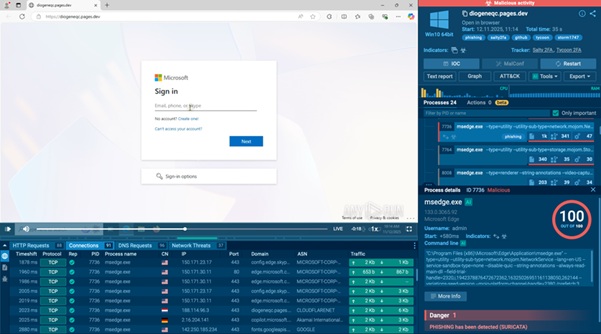
Hybrid phishkit attack discovered in 35 seconds inside ANY.RUN sandbox
This is exactly where many traditional controls fall short. Email filters may let the lure through, URL scanners often see only a harmless redirect, and authentication logs can still show what looks like a normal sign-in. By the time a case looks “real,” the session may already be stolen.
Top SOC teams have found a faster way to catch this class of attack: they run suspicious links through an interactive sandbox like ANY.RUN, then interact with the page to trigger the full flow and watch the chain unfold in real time.
|
Detect phishkit and malware activity in minutes instead of hours, reducing MTTR, lowering escalations, and preventing costly account takeover. |
In the enterprise-focused campaigns mentioned above, teams were able to expose the full attack chain in just 35 seconds. They observed Tycoon 2FA and Salty2FA operating in the same chain: one handled the initial lure and proxying, while the other took over later for credential capture, session hijacking, or follow-on delivery.
What makes this analysis fast and effective inside ANY.RUN:
- Interactive execution, not passive scanning: Teams can click through the flow like a real user, which triggers the exact redirects, proxy logic, and scripts phishkits try to hide.
- Full attack chain visibility in one place: You see where the link goes, what loads, what it calls out to, and how the phishing stage evolves across steps.
- Behavior-first evidence: Instead of guessing from a URL snapshot, the sandbox captures the real TTPs and confirms what the kit is doing during runtime.
- Automatic IOC extraction: Domains, URLs, IPs, and related artifacts are collected during analysis so teams can block and hunt immediately.
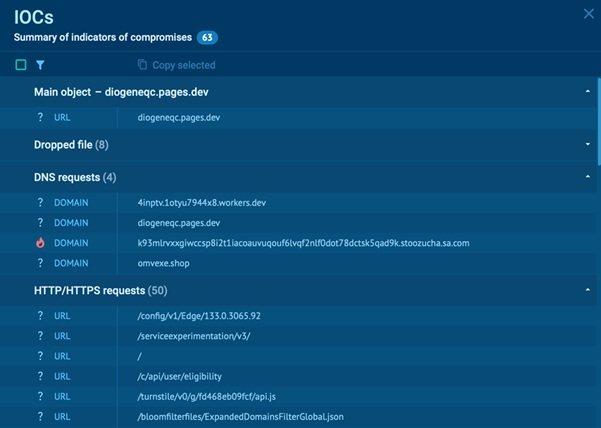
Related IOCs extracted from the analysis session inside ANY.RUN sandbox
- Auto-generated report: A ready-to-share summary of the session, indicators, and key findings for fast triage, escalation, and documentation.
- AI Assistant for clarity: Helps explain suspicious behaviors and highlights what matters most, especially when the flow is complex or multi-stage.
Stop Phishkits Before They Turn Into Breaches
Hybrid phishkits show how quickly modern phishing can move from a single click to full account compromise. When credential theft, MFA interception, and session hijacking happen in seconds, slow or partial visibility is no longer enough.
Security teams that catch these attacks early share one advantage: they see the real behavior as it happens. Interactive sandbox analysis helps confirm phishing activity, expose hidden proxy logic, and collect actionable indicators before attackers can expand access across the organization.
SOC teams that adopted ANY.RUN are already reporting measurable impact:
- 3× boost in SOC efficiency: More incidents handled with the same headcount, less overtime pressure, better SLA performance.
- 21 minutes shaved off MTTR per case: Smaller blast radius, fewer downstream systems affected, lower containment and recovery cost
- Around 30% fewer Tier-1 → Tier-2 escalations: Less time wasted on false positives, senior specialists stay focused on confirmed threats, lower operational spend per incident
Contact ANY.RUN experts to see how the interactive sandbox can fit into your workflows to speed up triage, reduce escalations, and stop account takeover before it turns into business impact.

