Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Technology
The Future is Hybrid: Practicing Security in the Hybrid Cloud
By now, many organizations have adopted the cloud in some way. We saw organizations moving whole servers over to the cloud at the beginning, but now we see small parts of a system being moved to the cloud and new cloud native offerings. We’ll use the analogies of Lincoln Logs and Legos to describe these deployment models.
Working Anywhere With Egnyte: Mobile Guide
In recent weeks, companies and organizations that ordinarily operate in a more “traditional” office environment have had to pivot quickly to flexible and alternative working arrangements. At Egnyte, our goal has always been to help provide safe, secure access to your content no matter where you are, and that goal has become increasingly more important in the current climate.
Use the Node.js HTTP Module to Make a Request
The ecosystem around making requests in Node.js applications is huge. With countless libraries available, it can be helpful to understand why they exist. This helps to improve your understanding of Node.js as a whole, and makes choosing an HTTP client easier. In the first post in this series, we looked at creating servers using Node's http module. In this post, we will explore making a request using the http.request method and handling the response.
Create a Server with the Node.js HTTP Module
Using Node.js on the web generally involves a server framework, like Express, Hapi, or Koa. These make working with the underlying HTTP support easier. Sometimes you need the full power of a framework, but in other cases that can be overkill. In this article, we'll ignore the benefits of a framework and look at the underlying features of Node's HTTP module and how you can use it to create a web server. In future articles, we'll examine other features of the HTTP module.
What COVID-19 teaches us about Micro-segmentation and Run-time Cloud Workload Protection
March 2020, the Coronavirus is pretty much everywhere. As I am writing these lines, the number of cases worldwide is 341,334 and 192 different countries have experienced infections.The world is fighting this epidemic and travel limitations are widely used in order to control the spread of the disease. While some say these restrictions are critical, others claim it to be ineffective and redundant. I am not an epidemiologist and will leave that analysis to the experts.
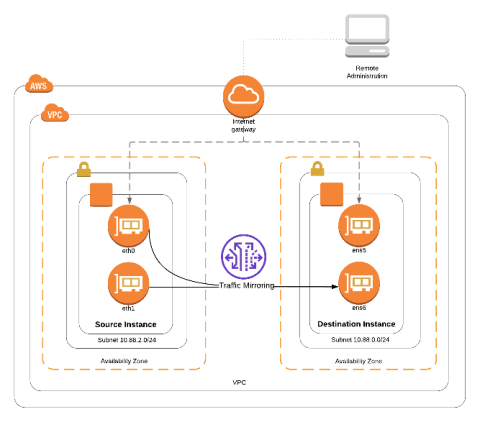
Amazon VPC Traffic Mirroring
Rezilion to bring autonomous cloud workload protection to VMware Tanzu Service Mesh
Security never rests. Especially at the speed and scale of cloud workloads. Have you heard that VMware announced our collaboration for bringing self-healing as a service for cloud-native workloads communicating via VMware Tanzu Service Mesh, built on VMware NSX? We’ve been getting a lot of questions on the topic and so consider this a first stab at spelling out what we’re doing with Tanzu Service Mesh. You can expect much more detail in the coming weeks.
API Monitoring: What should you measure?
When it comes to monitoring third-party APIs and web services, what you monitor is as important as how you monitor. Data is useful, but actionable data is where the true value is. Below we've listed the most common and valuable metrics to monitor when relying on third-party API integrations and web services.
A Message From the Founders
We’re excited to introduce Axis Security! Application access for employees, partners, and other stakeholders is an essential component of an efficient, modern organization. Axis Security emerged from stealth mode today to solve this problem with a new approach designed to make private application access amazingly simple.