Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
DevOps
Enforce Docker Image CIS Policy Compliance with Tripwire for DevOps
We are working hard adding features to our new Tripwire for DevOps service, initially announced at BlackHat 2018. If you are a loyal State of Security follower, last you read we added Auditing for Amazon Machine Images (aka AMIs). Today, we are introducing CIS policy compliance auditing for Docker images. Tripwire for DevOps allows you to evaluate your Docker Images to check for policy compliance at build time.
Auditing Amazon Machine Images with Tripwire for DevOps
Tripwire for DevOps continues to add new features and capabilities. The newest of these is the ability to perform vulnerability scans against Amazon Machine Images (AMIs) in the same Tripwire for DevOps workflow used for your Docker containers. This blog will discuss the creation of AMIs and how to audit them for vulnerabilities within Tripwire for DevOps.
Tripwire For DevOps External Registry And Alert Capability
Although many organizations are shifting security to the left and embracing the integration of security tools into their continuous integration / continuous delivery pipelines, there are others who have different wants and needs.
8 Surprising Facts About Real Docker Adoption
Complete Guide to Container Security
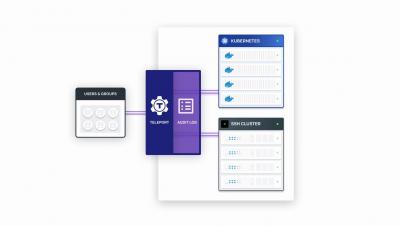
Teleport 3.0 Demo
What to Do and What to Avoid When Implementing Security in the DevOps Lifecycle
DevOps is redefining the way organizations handle software development. But it’s also challenging security professionals in their efforts to manage digital risk. With that said, there are security teams need to be strategic about how they approach DevOps security. Here are some expert recommendations on what to do and what to avoid when implementing security in the DevOps lifecycle.