Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Compliance
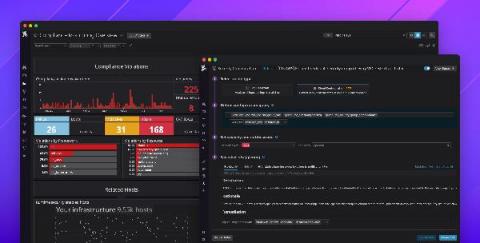
Introducing Datadog Compliance Monitoring
Governance, risk, and compliance (GRC) are major inhibitors for organizations moving to the cloud—and for good reason. Cloud environments are complex, and even a single misconfigured security group can result in a serious data breach. In fact, asset misconfigurations were the leading cause of cloud security breaches in 2019. This puts a lot of pressure on developer and operations teams to properly secure their services and maintain regulatory compliance.
What is FFIEC-CAT?
There has been a significant rise in the number and complexity of Cybersecurity threats over the last several years in the financial services industry. Institutions have been in need of a tool that can aid in identifying all the different risk types and how to develop a plan to be prepared for this continuously growing number of threats. Finally a tool has been developed for these intuitions, especially for Credit Unions.
Understanding the Benefits of the Capability Maturity Model Integration (CMMI)
Many organizations have Information Security Programs (ISPs), but many executives and boards do not know how to measure progress within these programs. They are therefore hesitant to believe any investment in technology will mitigate perceived or even unknown risks. Some organizations use regulated compliance standards such as PCI DSS or AICPA attestations as measures of their ISP.
Ditch the Checklist: Why Automation is the Key to Content Compliance
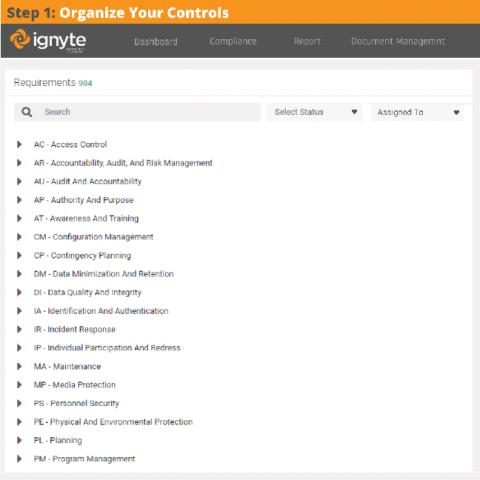
Compliance frameworks provide guidelines for effective and secure operations for content management across a company’s various repositories. They’re written as a set of controls, each one which corresponds to different settings and policies that an organization must follow in order to ensure the safety of their data.
Collect Evidence & Artifacts from people with Request Links
Controls management and assessments are critical for properly managing a complete information security program. Similarly, evidence collection, management, and approval is vital for proper control based security governance programs in any organization.
Netwrix Auditor for Active Directory - Overview
Netwrix Auditor for Windows File Servers - Overview
Understanding the Purpose of Security Controls and the Need for Compliance
What are the brakes on a car designed to do? I have asked this question many times when speaking to customers or organizations who were dipping their toes into the audit space. Invariably, their answer was, “To stop the car.” At this point, I would then ask, “Then how do you get where you want to go?”
ISO 27001 Requirements Checklist: Steps and Tips for Implementation
ISO 27001 enables organizations of any size to manage the security of assets such as employee information, financial information, intellectual property, employee details, and third-party information. ISO 27001 is primarily known for providing requirements for an information security management system (ISMS) and is part of a much larger set of information security standards. An ISMS is a standards-based approach to managing sensitive information to make sure it stays secure.