Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Cloud
IBM and Sysdig team up to extend security governance with IBM Cloud Pak for Multicloud Management
Sysdig, an industry leader for monitoring and security of cloud-native workloads, and IBM have joined forces to bring a fully Integrated powerful platform that delivers the security and performance that enterprises need in today’s multi-cloud world. Sysdig Secure and the IBM Cloud Pak for Multicloud Management (MCM) can help you accelerate Kubernetes and cloud adoption by addressing security and regulatory compliance from the start on enterprise hybrid cloud environments.
Black Duck SCA & Coverity Static Analysis (SAST) Integrations with Amazon AWS CI Tools | Synopsys
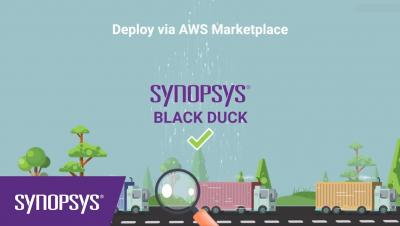
10 Alerts and Visualizations for S3 Server Access Logs to take control of AWS infrastructure
AWS S3 Server Access logs provide detailed records for requests made to S3 buckets. They’re useful for many applications. For example, access log information can be useful in security and access audits. It can also help generate customer insights and better understand your Amazon S3 bill. Coralogix makes it easy to integrate with your S3 server access logs via a Lambda function.
2019 in Review: From Product-Market Fit to Series A to Company Scale
2019 has been a year of metamorphosis for Gravitational. We started over four years ago as a group of infrastructure engineers who were frustrated with the complexity of cloud application delivery. We wanted cloud apps to be as easy to distribute as desktop software is. It was a big year for our team.
Key Cloud Security Challenges and Strategies to Overcome Them
The cloud has changed how we use and consume IT services. Where data resides along with how it is transferred, stored and processed has fundamentally changed and with-it new risk management challenges. Let’s talk about some of those challenges. First and foremost, the cat is out of the bag. We’re not going back to the data center, and any resistance to that is going to be seen as a business inhibitor and will therefore not get much airtime.
Cloud Migration: Moving Your Security Mindset Along with Your Data
Migrating our data to the cloud to digitally transform and streamline your IT environment is easier than ever. Cloud security is in a place where it is stronger than on-premise security and The Big Three – AWS, Microsoft, and Google – have more access to resources and personnel than you can ever dream of. For infrastructure security, they’re the best. So why are so many companies still concerned with moving their data to the cloud?
DevOps: 8 Reasons for DevOps to Use a Binary Repository Manager on the Cloud
Teleport 4.2 - Enhanced Session Recording, Workflows, and GCP
Teleport 4.2 delivers a strong foundation of new features. We have a full list of improvements and fixes attached to our Teleport 4.2.0 GitHub release. Below are a couple of the highlights. Teleport now provides greater visibility into what’s happening during a Teleport session with our Enhanced Session Recording. We’ve also laid the groundwork for a world of possibilities with our enterprise-only Role Escalation via a Workflows API.
Malware in the Cloud: Protecting Yourself Based on Your Cloud Environment
In some ways, the cloud has made security management easier, as many cloud providers have taken the responsibilities traditionally associated with local server management out of your hands. But in other ways, the security management conversation has become more confusing for decision makers, as “cloud” is a very broadly defined term and could speak to a variety of different technology ecosystems with their own security considerations.