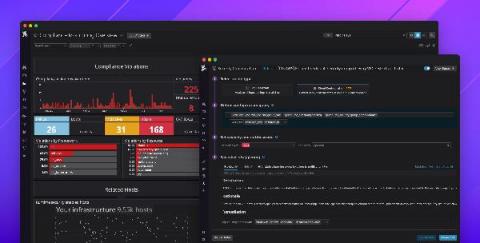
Monitor AWS FSx audit logs with Datadog
Amazon FSx for Windows File Server is a fully managed file storage service built on Windows Server. Migrating on-premise Windows file systems to a managed service like FSx enables organizations to reduce operational overhead and take advantage of the flexibility and scalability of the cloud. But having visibility into file access activity across their environment is key for security and compliance requirements, particularly in sectors such as financial services and healthcare.