Splunking Slack Audit Data
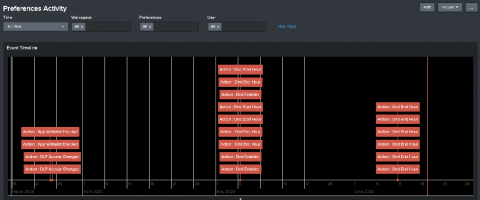
The Slack Audit Logs API is for monitoring the audit events happening in a Slack Enterprise Grid organization to ensure continued compliance, to safeguard against any inappropriate system access, and to allow the user to audit suspicious behavior within the enterprise. This essentially means it is an API to know who did what and when in the Slack Enterprise Grid account. We are excited to announce the Slack Add-on for Splunk, that targets this API as a brand new data source for Splunk.