Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Threat Intelligence
Trustwave's Action Response: Russia-Ukraine Crisis - Defending Your Organization From Geopolitical Cybersecurity Threats
Trustwave security and engineering teams are on heightened alert and are actively monitoring malicious cyber activity associated with and adjacent to the escalating military conflict between Russia and Ukraine. Trustwave is working closely with its clients around the world to enhance cyber preparedness during this time.
What is Cyber Threat Intelligence? Think like a Cybercriminal
Cyber threat intelligence (CTI) considers the full context of a cyber threat to inform the design of highly-targeted defensive actions. CTI combines multiple factors, including the motivations of cybercriminals and Indicators of Compromise (IOC), to help security teams understand and prepare for the challenges of an anticipated cyber threat.
Cyberattacks are Evolving. How to Accelerate Detection and Response with ThreatQ
You don’t have to look far for proof that cybercrime is soaring to new heights. Early in the pandemic the U.N. reported cybercrime had increased 600% and other experts estimate damages from global cybercrime to reach $10.5 trillion annually by 2025, up from $3 trillion in 2015. Last year alone, we started 2021 in the fog of the SolarWinds attack and finished with the infamous Log4j vulnerabilities, the full impact of which will take years to understand.
CrowdStrike's Annual Threat Report Reveals Uptick Around Ransomware and Disruptive Operations; Exposes Evolution of eCrime Ecosystem
Combat Advanced Threats with a Multi-disciplinary Threat Intelligence Program
Ransomware attacks on Colonial Pipeline, JBS Foods and Kronos are just a few recent examples in the rise of cyber-physical attacks that disrupt lives of individuals and have the potential to cause physical harm. This concerning trend is capturing the attention of organizations worldwide, with Gartner predicting that 75% of CEOs will be personally liable for cyber-physical security incidents by 2024.
You Don't Have to Fall for the "Tinder Swindler" to Get Cheated this Valentine's Day
The “Tinder Swindler” is an extreme example of how online scammers can mask their identity, charm their victims and bilk them of millions of dollars, but the point is made. Whether you’re looking for love this Valentine’s Day or wanting to show your loved ones how much you appreciate them, beware of online scams. Some of the latest involve gift cards, where scammers who have honed their craft and done their homework about you, ask for payment in the form of gift cards.
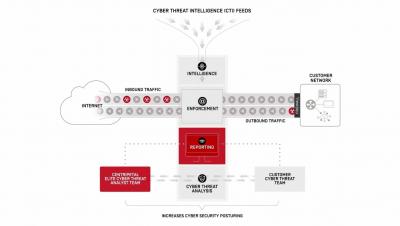
How Centripetal CleanINTERNET Works
The state of the SOC: skills shortages, automation and gaining context remain a challenge for SOCs
The security operations center (SOC) has been on the front line facing the pandemic-induced escalation of cybersecurity threats in the past eighteen months. A 2020 study by Forrester found that the average security operations team receives more than 11,000 alerts per day and that figure is likely to have grown in the intervening period. While they were deeply engaged responding to the crisis, SOC teams were simultaneously facing the disruption common to all formerly office-based workers.
Threat Advisory: STRT-TA02 - Destructive Software
The Splunk Threat Research Team is monitoring open channel intelligence and government alerts indicating the possibility of malicious campaigns using destructive software in relation to ongoing geopolitical events. Based on historical data of named geopolitical actors, the use of destructive payloads has been observed in past campaigns.